- Corpus ID: 212469884

4G Wireless Technology: A Brief Review
- Ashish Kumar , Ankit Aswal , L. Singh
- Published 2013
- Engineering, Computer Science
Figures and Tables from this paper

7 Citations
Study on call admission control schemes in 3gpp lte network, deep learning autoencoder based anomaly detection model on 4g network performance data, ehealth: a survey of architectures, developments in mhealth, security concerns and solutions, effect of internet use on medical students before and after 4g internet service in india: a comparative study., ubiquitous flipped classroom instructional model with learning process of scientific to enhance problem-solving skills for higher education (ufc-ps model), advances in fronthauling of communication technologies: a review, monografía internet de las cosas: modelos de comunicación, desafíos y aplicaciones., 14 references, international journal of computer science and technology 201, 4g wireless technology: when will it happen what does it offer, beyond 3g: 4g mobile communication, 4g wireless networks: benefits and challenges.
- Highly Influential
- 10 Excerpts
The software radio concept
3gpp long term evolution: a technical overview, lte for umts - ofdma and sc-fdma based radio access, fundamentals of wimax: understanding broadband wireless networking, 3gpp long term evolution, overview of handoff schemes in cellular mobile networks and their comparative performance evaluation, related papers.
Showing 1 through 3 of 0 Related Papers
Evolution of Wireless Communications with 3G, 4G, 5G, and Next Generation Technologies in India
- Conference paper
- First Online: 29 January 2021
- Cite this conference paper

- Pranay Yadav 38 ,
- Alok Upadhyay 39 ,
- V. B. Surya Prasath 40 ,
- Zakir Ali 41 &
- Bharat Bhooshan Khare 42
Part of the book series: Lecture Notes in Electrical Engineering ((LNEE,volume 709))
Included in the following conference series:
- International Conference on Emerging Trends and Advances in Electrical Engineering and Renewable Energy
885 Accesses
17 Citations
In the era of wireless communication, internet devices such as smart phones, hotspots, and Wi-Fi zone are important player of rapid growth of data usage. Internet connection devices are building new challenges for internet service providers such as higher bandwidth and indomitable increasing users day to day. This article gives an overview of existing different technologies of wireless communication as well as future enhancement of wireless services is explained. Different techniques during last decade are introduced for handling next generation techniques for ISPs. We provided a comparative analysis of different generations such as 3G, 4G, and 5G, and we focus on the next generation communication technologies 6G and 7G. Current research works are focused on 5G and next era generation of communication technologies. The development of internet infrastructure is essential for better mobile broadband experiences. In this work, we compared all the available generation communication systems, either wireless or wired, that are being deployed as well as future directions.
This is a preview of subscription content, log in via an institution to check access.
Access this chapter
- Available as PDF
- Read on any device
- Instant download
- Own it forever
- Available as EPUB and PDF
- Compact, lightweight edition
- Dispatched in 3 to 5 business days
- Free shipping worldwide - see info
- Durable hardcover edition
Tax calculation will be finalised at checkout
Purchases are for personal use only
Institutional subscriptions
Lin, Y.-B., Lin, P.-J., Sung, Y. C., Chen, Y.-K., & Chen, W.-E. (2013). Performance measurements of TD-LTE, WiMAX and 3G systems. In IEEE Wireless Communications , June 2013.
Google Scholar
Pareit, D., et al. (2010). A throughput analysis at the MAC layer of mobile WiMAX. In Wireless Commun. and Net. Conf. (WCNC) , Apr. 2010.
Westall, J. M., & Martin, J. J. (2011). Performance characteristics of an oprational WiMAX network. IEEE Transactions Mobile Computing, 10 (7), 941–953.
Article Google Scholar
Sarma, A., Chakraborty, S., & Nandi, S. (2016). Deciding handover points based on context-aware load balancing in a WiFi-WiMAX heterogeneous network environment. IEEE Transactions on Vehicular Technology, 65 (1), January 2016.
Sapakal, R. S., & Kadam, S. S. (2013). 5G mobile technology. International Journal of Advanced Research in Computer Engineering & Technology (IJARCET), 2 ,(2), February 2013.
Sharma, P., Verma, M., Sundriyal, N., & Chauhan, J. (2014). 5G mobile wireless technology. International Journal of Research (IJR), 1 (9), October 2014, ISSN 2348-6848.
Gupta, & Jha, R. K. (2015). A survey of 5G network: Architecture and emerging technologies. IEEE Access, 3 , 28.
Singh, A. P., Nigam, S., Gupta, N. K. (2016). A study of next generation wireless network 6G. International Journal of Innovative Research in Computer and Communication Engineering, 4 (1), January 2016.
Lin, Y.-B., & Alrajeh, N. (2012). Mobile telecommunications and applications to healthcare network . Kingdom of Saudi Arabia: Speech at King Abdulaziz City for Science and Technology.
Niyato, D., & Hossain, E. (2007). Wireless broadband access: WiMAX and beyond-integration of WiMAX and WiFi: Optimal pricing for bandwidth sharing. IEEE Communications Magazine, 45 (5), 140–146.
Wang, W., Liu, X., Vicente, J., & Mohapatra, P. (2011). Integration gain of heterogeneous WiFi/WiMAX networks. IEEE Transactions Mobile Comput, 10 (8), 1131–1143.
Meier, R. C., Dettloff, K., & Waclawsky, J. G. (2013). System and method for integrated WiFi/WiMAX neighbor AP discovery and AP advertisement . U.S. Patent 20 130 070 641, Mar. 21, 2013.
Lim, W.-S., Kim, D.-W., Suh, Y.-J., & Won, J.-J. (2009). Implementation and performance study of IEEE 802.21 in integrated IEEE 802.11/802.16e networks. Computer Communications, 32 (1), 134–143.
Kiran Gowda, H. N., Kusuma, M., & Udaya Kumar, C. (2013). A comprehensive study on 4G broadband networks: WiMAX and LTE. International Journal of Advanced Research in Computer and Communication Engineering, 2 (9), September 2013.
Abbas Ali, M., & Barakabitze, A. A. (2015). Evolution of LTE and related technologies towards IMT-advanced. International Journal of Advanced Research in Computer Science and Software Engineering, 5 (1), January 2015.
Yadav, P., Sharma, S., Tiwar, P., Prasad, M., Mohanty, S. P., & Puthal, D. (2018). A modified link consistency based routing protocol to prevent wormhole attacks in IoT. In IEEE, Consumer Electronics .
Yaday, P., Sharma, S., Tiwari, P., Prasad, M., & Mohanty, S. P. A system design for IoT based smart sensing and auto controlling for smart residence. IEEE Access (Under Review).
Yadav, P., Sharma, S., Tiwari, P., Dey, N., Ashour, A. S., & Nguyen, G. N. A Modified Hybrid Structure for Next Generation Super High Speed Communication Using TDLTE and Wi-Max . Accepted for publication in Studies in Big Data, Springer Book Chapter (Web of Science) 2017.
Download references
Author information
Authors and affiliations.
R&D, Ultra-Light Technology, Bhopal, India
Pranay Yadav
Quality Officer Vodaphone Idea Limited, Indore, MP, India
Alok Upadhyay
Division of Biomedical Informatics, Cincinnati Children’s Hospital Medical Center, Cincinnati, USA
V. B. Surya Prasath
Department of Electronics & Communication Engineering, IET, Bundelkhand University, Jhansi, India
Department of Electrical Engineering, UIT, Bhopal, MP, India
Bharat Bhooshan Khare
You can also search for this author in PubMed Google Scholar
Corresponding author
Correspondence to Pranay Yadav .
Editor information
Editors and affiliations.
School of Computer Engineering, Kalinga Institute of Industrial Technology (KIIT Deemed to be University), Bhubaneswar, Odisha, India
Pradeep Kumar Mallick
Department Electrical and Electronics Engineering, Sikkim Manipal Institute of Technology, Rangpo, Sikkim, India
Akash Kumar Bhoi
Division of Information and Communication, Baekseok University, Cheonan, Ch’ungch’ong-namdo, Korea (Republic of)
Gyoo-Soo Chae
Vel Tech Rangarajan Dr. Sagunthala R&D Institute of Science and Technology, Chennai, Tamil Nadu, India
Kanak Kalita
Rights and permissions
Reprints and permissions
Copyright information
© 2021 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper.
Yadav, P., Upadhyay, A., Prasath, V.B.S., Ali, Z., Khare, B.B. (2021). Evolution of Wireless Communications with 3G, 4G, 5G, and Next Generation Technologies in India. In: Mallick, P.K., Bhoi, A.K., Chae, GS., Kalita, K. (eds) Advances in Electronics, Communication and Computing. ETAEERE 2020. Lecture Notes in Electrical Engineering, vol 709. Springer, Singapore. https://doi.org/10.1007/978-981-15-8752-8_35
Download citation
DOI : https://doi.org/10.1007/978-981-15-8752-8_35
Published : 29 January 2021
Publisher Name : Springer, Singapore
Print ISBN : 978-981-15-8751-1
Online ISBN : 978-981-15-8752-8
eBook Packages : Computer Science Computer Science (R0)
Share this paper
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Publish with us
Policies and ethics
- Find a journal
- Track your research
Academia.edu no longer supports Internet Explorer.
To browse Academia.edu and the wider internet faster and more securely, please take a few seconds to upgrade your browser .
Enter the email address you signed up with and we'll email you a reset link.
- We're Hiring!
- Help Center

2G-4G Networks: Evolution of Technologies, Standards, and Deployment

2010, Encyclopedia of Multimedia Technology and …
Related Papers
Wasim Sulehria
International Journal IJRITCC
Cellular technology is the foundation of mobile wireless communications and supports users in locations that are not easily served by wired networks. Cellular technology is the underlying technology for mobile telephones, personal communications systems, wireless Internet and wireless Web applications, and much more. This article looks at how cellular technology has evolved through four generations and is poised for a fifth generation.
Xahara Eliya
Dragan Manevski
Garlapati Raviteja
srishti pathak
Shubham Dethe
Karamdeep Singh , Shivinder Devra
The need and demand of mobile and internet is increasing every day. Creation of technology and evolution of mobile industry has been initiated by mobile industry since early 1970s. First generation only provided voice communication facility, whereas second generation provided voice as well as data services. Further with more advancements in mobile wireless technology 3G provided us with video conferencing and etc. With increasing demand 4G came into existence and provided us with ultra-broadband internet access. 5G will be able to provide us facilities that one has never experienced till date. Our diversity of culture also plays a crucial role for this tremendous growth of mobile technology as they adopted this technology in friendly manner.
Ahmedul Haque
1. 5G technologies will change the way most high-bandwidth users access their phones. With 5G pushed over a VOIP-enabled device, people will experience a level of call volume and data transmission never experienced before.5G technology is offering the services in Product Engineering, Documentation, supporting electronic transactions (e-Payments, e-transactions) etc. As the customer becomes more and more aware of the mobile phone technology, he or she will look for a decent package all together, including all the advanced features a cellular phone can have. Hence the search for new technology is always the main motive of the leading cell phone giants to out innovate their competitors. Recently apple has produced shivers all around the electronic world by launching its new handset, the I-phone. Features that are getting embedded in such a small piece of electronics are huge.
American journal of Engineering Research (AJER)
This paper is focused on the specification of future generations of wireless mobile communication networks. The paper throws light on the evolution and development of various generations of mobile wireless technology along with their significance and advantages of one over the other. 5G technologies will change the way most high-bandwidth users access their phones. With 5G people will experience a level of call volume and data transmission never experienced before. 5G technology is offering the services in different fields like Documentation, supporting electronic transactions (e-Payments, e-transactions) etc. As the customer becomes more and more aware of the mobile phone technology, he or she will look for a decent package all together, including all the advanced features a cellular phone can have. The 5G design is based on user-centric mobile environment with many wireless and mobile technologies on the ground. WWWW that is World Wide Wireless Web allows complete wireless communication with almost no limitation, Multi-Media Newspapers, watch TV programs with the clarity as to that of an HD TV.
Loading Preview
Sorry, preview is currently unavailable. You can download the paper by clicking the button above.
RELATED PAPERS
Rahul Anand
Dan-jumbo Idaerefagha
Maheshkumar Sahu
Mian Ahmad Jan Palosa Campus AWKUM
IOSR Journals
Anish Mathews
IJRCAR JOURNAL
Independent IJCEROnline
Franklin Aditama Katoende
Iwan Krisnadi , Hartana Hartana
BIPUL KUMAR GUPTA
DIMAS HENDRATNO
ashwani kumar
virendra singh
Qammar Zaman
Abdulmajeed Ali Al Jabri
OBAIDALLAH ELSHAFIEY
Ilmah Rafia
Thayalan Ramasamy
Ahmed suliman
Carlos Negronomicón
IJCSMC Journal
Surbhi Mainde
Krishna Prasad K (Self Published)
Krishna Prasad
Ijariit Journal
Animesh Sonwane
The Ijes The Ijes
Samuel Ajayi
Innovative Research Publications
IJSTE - International Journal of Science Technology and Engineering
Darshan Lal
Shaik Mahaboob Subani
Bechtel Telecommunications Technical Journal
Tanu Jindal
MOHAMMAD ARIFIN RAHMAN KHAN
Agomuo Uchechukwu
- We're Hiring!
- Help Center
- Find new research papers in:
- Health Sciences
- Earth Sciences
- Cognitive Science
- Mathematics
- Computer Science
- Academia ©2024
IEEE Account
- Change Username/Password
- Update Address
Purchase Details
- Payment Options
- Order History
- View Purchased Documents
Profile Information
- Communications Preferences
- Profession and Education
- Technical Interests
- US & Canada: +1 800 678 4333
- Worldwide: +1 732 981 0060
- Contact & Support
- About IEEE Xplore
- Accessibility
- Terms of Use
- Nondiscrimination Policy
- Privacy & Opting Out of Cookies
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. © Copyright 2024 IEEE - All rights reserved. Use of this web site signifies your agreement to the terms and conditions.
Information
- Author Services
Initiatives
You are accessing a machine-readable page. In order to be human-readable, please install an RSS reader.
All articles published by MDPI are made immediately available worldwide under an open access license. No special permission is required to reuse all or part of the article published by MDPI, including figures and tables. For articles published under an open access Creative Common CC BY license, any part of the article may be reused without permission provided that the original article is clearly cited. For more information, please refer to https://www.mdpi.com/openaccess .
Feature papers represent the most advanced research with significant potential for high impact in the field. A Feature Paper should be a substantial original Article that involves several techniques or approaches, provides an outlook for future research directions and describes possible research applications.
Feature papers are submitted upon individual invitation or recommendation by the scientific editors and must receive positive feedback from the reviewers.
Editor’s Choice articles are based on recommendations by the scientific editors of MDPI journals from around the world. Editors select a small number of articles recently published in the journal that they believe will be particularly interesting to readers, or important in the respective research area. The aim is to provide a snapshot of some of the most exciting work published in the various research areas of the journal.
Original Submission Date Received: .
- Active Journals
- Find a Journal
- Proceedings Series
- For Authors
- For Reviewers
- For Editors
- For Librarians
- For Publishers
- For Societies
- For Conference Organizers
- Open Access Policy
- Institutional Open Access Program
- Special Issues Guidelines
- Editorial Process
- Research and Publication Ethics
- Article Processing Charges
- Testimonials
- Preprints.org
- SciProfiles
- Encyclopedia

Article Menu

- Subscribe SciFeed
- Recommended Articles
- Google Scholar
- on Google Scholar
- Table of Contents
Find support for a specific problem in the support section of our website.
Please let us know what you think of our products and services.
Visit our dedicated information section to learn more about MDPI.
JSmol Viewer
Impact of 3g and 4g technology performance on customer satisfaction in the telecommunication industry.

1. Introduction
1.1. the cellular communication evaluation and technologies, 1.1.1. 1g technology, 1.1.2. 2g technology, 1.1.3. 3g technology, 1.1.4. 4g technology, 1.1.5. 5g technology, 1.2. machine learning (ml) techniques for the wireless communications, 1.3. big data analysis in wireless communication, 1.4. contributions of our study, 2. related work, 2.1. theoretical framework, 2.2. hypotheses of the study, 3. research methodology, 3.1. variables and target population, 3.2. questionnaire and treatment of scales, 3.3. data collection procedure, 4. results and analysis, 4.1. descriptive statistics, 4.1.1. demographics, network sim connection type, telecom operators in punjab pakistan, cities using the internet, 4.2. data analysis techniques (data screening), 4.3. level of analysis, 4.4. reliability and validity, 4.5. discriminant validity, 4.6. path coefficient (β), 5. discussion, 5.1. conclusions, 5.2. future research directions.
- Data collection in this study can be extended to the whole country with a high number of responses to make the results more reliable.
- This study can further extend the impact of 5G technology network performance on customer satisfaction in a different area because 5G is expected to come in the next couple of years.
- Another recommendation about this study is to extend this study compassion based on 3G and 4G services with different telecom operators who are providing the best services in the telecom sector
- We will also conduct our research study on 5G technology.
Author Contributions
Data availability statement, acknowledgments, conflicts of interest.
- Pakistan Telecommunication Authority. Telecom Indicators. Available online: https://www.pta.gov.pk/en/telecom-indicators (accessed on 18 July 2022).
- Jere, M.G.; Mukupa, A. Customer satisfaction and loyalty drivers in the Zambian mobile telecommunications industry. J. Bus. Retail Manag. Res. 2018 , 13 , 120–128. [ Google Scholar ] [ CrossRef ] [ Green Version ]
- Selelo, G.B.; Lekobane, K.R. Effects of service quality on customers satisfaction on Botswana’s mobile telecommunications industry. Arch. Bus. Res. 2017 , 5 , 212–228. [ Google Scholar ]
- Chee, V.S.; Husin, M.M. The Effect of Service Quality, Satisfaction and Loyalty toward Customer Retention in the Telecommunication Industry. Int. J. Acad. Res. Bus. Soc. Sci. 2020 , 10 , 55–71. [ Google Scholar ]
- Marvelous, M.; Asphat, M.; Malon, S.R. The influence of customer-based brand equity on customer satisfaction and brand loyalty: Evidence from South African Mobile Telecommunications Industry. Int. J. Bus. Manag. Stud. 2019 , 11 , 32–47. [ Google Scholar ]
- Gawas, A.U. An overview on evolution of mobile wireless communication networks: 1G–6G. Int. J. Recent Innov. Trends Comput. Commun. 2015 , 3 , 3130–3133. [ Google Scholar ]
- Pereira, V.; Sousa, T. Evolution of Mobile Communications: From 1G to 4G. Dep. Inform. Eng. Univ. Coimbra Port. 2004 , 4 , 20. [ Google Scholar ]
- Agarwal, A.; Misra, G.; Agarwal, K. The 5th generation mobile wireless networks-key concepts, network architecture and challenges. Am. J. Electr. Electron. Eng. 2015 , 3 , 22–28. [ Google Scholar ]
- Waleed, S.; Ullah, I.; Khan, W.U.; Rehman, A.U.; Rahman, T.; Li, S. Resource allocation of 5G network by exploiting particle swarm optimization. Iran J. Comput. Sci. 2021 , 4 , 211–219. [ Google Scholar ] [ CrossRef ]
- Khan, W.U.; Imtiaz, N.; Ullah, I. Joint optimization of NOMA-enabled backscatter communications for beyond 5G IoT networks. Internet Technol. Lett. 2021 , 4 , e265. [ Google Scholar ] [ CrossRef ]
- Mazhar, T.; Malik, M.A.; Haq, I.; Rozeela, I.; Ullah, I.; Khan, M.A.; Adhikari, D.; Ben Othman, M.T.; Hamam, H. The Role of ML, AI and 5G Technology in Smart Energy and Smart Building Management. Electronics 2022 , 11 , 3960. [ Google Scholar ] [ CrossRef ]
- Aldossari, S.M.; Chen, K.-C. Machine learning for wireless communication channel modeling: An overview. Wirel. Pers. Commun. 2019 , 106 , 41–70. [ Google Scholar ] [ CrossRef ]
- Jagannath, J.; Polosky, N.; Jagannath, A.; Restuccia, F.; Melodia, T. Machine learning for wireless communications in the Internet of Things: A comprehensive survey. Ad. Hoc. Netw. 2019 , 93 , 101913. [ Google Scholar ] [ CrossRef ] [ Green Version ]
- Li, C.; Cao, Z. Lora networking techniques for large-scale and long-term iot: A down-to-top survey. ACM Comput. Surv. (CSUR) 2022 , 55 , 1–36. [ Google Scholar ] [ CrossRef ]
- Lin, Y.; Song, H.; Ke, F.; Yan, W.; Liu, Z.; Cai, F. Optimal caching scheme in D2D networks with multiple robot helpers. Comput. Commun. 2022 , 181 , 132–142. [ Google Scholar ] [ CrossRef ]
- Guo, L.; Ye, C.; Ding, Y.; Wang, P. Allocation of centrally switched fault current limiters enabled by 5G in transmission system. IEEE Trans. Power Deliv. 2020 , 36 , 3231–3241. [ Google Scholar ] [ CrossRef ]
- Alsheikh, M.A.; Niyato, D.; Lin, S.; Tan, H.-P.; Han, Z. Mobile big data analytics using deep learning and apache spark. IEEE Netw. 2016 , 30 , 22–29. [ Google Scholar ] [ CrossRef ] [ Green Version ]
- Bi, S.; Zhang, R.; Ding, Z.; Cui, S. Wireless communications in the era of big data. IEEE Commun. Mag. 2015 , 53 , 190–199. [ Google Scholar ] [ CrossRef ] [ Green Version ]
- Huang, J.; Wang, C.-X.; Bai, L.; Sun, J.; Yang, Y.; Li, J.; Tirkkonen, O.; Zhou, M.-T. A big data enabled channel model for 5G wireless communication systems. IEEE Trans. Big Data 2018 , 6 , 211–222. [ Google Scholar ] [ CrossRef ] [ Green Version ]
- Stergiou, C.L.; Plageras, A.P.; Psannis, K.E.; Gupta, B.B. Secure machine learning scenario from big data in cloud computing via internet of things network. In Handbook of Computer Networks and Cyber Security ; Gupta, B., Perez, G., Agrawal, D., Gupta, D., Eds.; Springer: Cham, Switzerland, 2020. [ Google Scholar ] [ CrossRef ]
- Mazhar, T.; Malik, M.A.; Mohsan, S.A.H.; Li, Y.; Haq, I.; Ghorashi, S.; Karim, F.K.; Mostafa, S.M. Quality of Service (QoS) Performance Analysis in a Traffic Engineering Model for Next-Generation Wireless Sensor Networks. Symmetry 2023 , 15 , 513. [ Google Scholar ] [ CrossRef ]
- Chang, Z.; Lei, L.; Zhou, Z.; Mao, S.; Ristaniemi, T. Learn to cache: Machine learning for network edge caching in the big data era. IEEE Wirel. Commun. 2018 , 25 , 28–35. [ Google Scholar ] [ CrossRef ]
- Qin, X.; Liu, Z.; Liu, Y.; Liu, S.; Yang, B.; Yin, L.; Liu, M.; Zheng, W. User OCEAN personality model construction method using a BP neural network. Electronics 2022 , 11 , 3022. [ Google Scholar ] [ CrossRef ]
- Hajar, M.A.; Alkahtani, A.A.; Ibrahim, D.N.; Al-Sharafi, M.A.; Alkawsi, G.; Iahad, N.A.; Darun, M.R.; Tiong, S.K. The Effect of Value Innovation in the Superior Performance and Sustainable Growth of Telecommunications Sector: Mediation Effect of Customer Satisfaction and Loyalty. Sustainability 2022 , 14 , 6342. [ Google Scholar ] [ CrossRef ]
- Shava, H. The relationship between service quality and customer satisfaction in the South African mobile network telecommunications industry. J. Int. Stud. 2021 , 14 , 70–83. [ Google Scholar ] [ CrossRef ]
- Shahzad, A.; Yaqub, R.M.S.; Di Vaio, A.; Hassan, R. Antecedents of customer loyalty and performance improvement: Evidence from Pakistan’s telecommunications sector. Util. Policy 2021 , 70 , 101208. [ Google Scholar ] [ CrossRef ]
- Mohammed, B.I.; Andavar, V. Customer Satisfaction towards Telecommunication mobile services: A case study in Asiacell Telecommunications in Sulaymaniyah city. Sci. J. Cihan Univ. Sulaimaniya 2022 , 6 , 173–184. [ Google Scholar ]
- Almuqren, L.; Cristea, A.I. Predicting STC Customers’ Satisfaction Using Twitter. IEEE Trans. Comput. Soc. Syst. 2022 , 10 , 204–210. [ Google Scholar ] [ CrossRef ]
- Al-Shammari, M.M.; AlShowaikh, A.F. Investigating user satisfaction of customer relationship management in a Telecommunications company in the kingdom of Bahrain. Int. J. Ebusiness Egovernment Stud. 2021 , 13 , 97–116. [ Google Scholar ]
- Shava, H. Service quality and customer satisfaction experience among south african mobile telecommunications consumers. Eurasian J. Bus. Manag. 2021 , 9 , 217–232. [ Google Scholar ] [ CrossRef ]
- Awadhi, J.; Obeidat, B.; Alshurideh, M. The impact of customer service digitalization on customer satisfaction: Evidence from telecommunication industry. Int. J. Data Netw. Sci. 2021 , 5 , 815–830. [ Google Scholar ]
- Shrivastava, N.; Limaye, M. A comparative study of customer satisfaction towards 4g service providers in bhopal division involving demographic variables. Int. J. Manag. (IJM) 2020 , 11 , 889–896. [ Google Scholar ]
- Ali, B.J.; Saleh, P.F.; Akoi, S.; Abdulrahman, A.A.; Muhamed, A.S.; Noori, H.N.; Anwar, G. Impact of Service Quality on the Customer Satisfaction: Case study at Online Meeting Platforms. In Ali, BJ, Saleh, Akoi, S., Abdulrahman, AA, Muhamed, AS, Noori, HN, Anwar, G. Impact of Service Quality on the Customer Satisfaction: Case study at Online Meeting Platforms. Int. J. Eng. Bus. Manag. 2021 , 5 , 65–77. [ Google Scholar ]
- Inegbedion, H.; Obadiaru, E. Modelling brand loyalty in the Nigerian telecommunications industry. J. Strateg. Mark. 2019 , 27 , 583–598. [ Google Scholar ] [ CrossRef ]
- Dhasan, D.; Kowathanakul, S. The impact of service quality, promotions and customer engagement in determining customer loyalty in the Thai mobile network industry. ABAC J. 2021 , 41 , 209–240. [ Google Scholar ]
- Laghari, A.A.; He, H.; Shafiq, M.; Khan, A. Application of quality of experience in networked services: Review, trend & perspectives. Syst. Pract. Action Res. 2019 , 32 , 501–519. [ Google Scholar ]
- Kubasu, K. Factors Influencing Customer Satisfaction with Services Offered by Safaricom Mobile Cellular Network ; Strathmore University: Nairobi, Kenya, 2018. [ Google Scholar ]
- Khan, N.; Akram, M.U.; Shah, A.; Khan, S.A. Calculating customer experience management index for telecommunication service using genetic algorithm based weighted attributes. In Proceedings of the 2018 IEEE International Conference on Innovative Research and Development (ICIRD), Bangkok, Thailand, 11–12 May 2018; pp. 1–8. [ Google Scholar ]
- Mahrinasari, M.; Pandjaitan, D.H.R. Moderating role of “consumer characteristics” in the influence of customer satisfaction on loyalty. In The Future Opportunities and Challenges of Business in Digital Era 4.0 ; Routledge: Oxfordshire, UK, 2020; pp. 205–209. [ Google Scholar ]
- Mohammed, S.S.; Shahin, O. Service quality perspectives in telecommunication sector: Trust and loyalty investigation. Amazon. Investig. 2020 , 9 , 394–403. [ Google Scholar ] [ CrossRef ]
- Zhou, R.; Wang, X.; Shi, Y.; Zhang, R.; Zhang, L.; Guo, H. Measuring e-service quality and its importance to customer satisfaction and loyalty: An empirical study in a telecom setting. Electron. Commer. Res. 2019 , 19 , 477–499. [ Google Scholar ] [ CrossRef ]
- Chun, L.; Tham, J.; Azam, S.F. Corporate competence determining factors in china telecom industry in achieving customer satisfaction. Eur. J. Manag. Mark. Stud. 2019 , 4 . [ Google Scholar ] [ CrossRef ]
- Ali, F.; Rasoolimanesh, S.M.; Sarstedt, M.; Ringle, C.M.; Ryu, K. An assessment of the use of partial least squares structural equation modeling (PLS-SEM) in hospitality research. Int. J. Contemp. Hosp. Manag. 2018 , 30 , 514–538. [ Google Scholar ] [ CrossRef ] [ Green Version ]
- Coakes, S.J.; Steed, L.; Dzidic, P. SPSS 13.0 for Windows: Analysis without Anguish ; John Wiley & Sons: Milton, QLD, Australia, 2006; 270p, ISBN 9780470809143 0470809140. [ Google Scholar ]
- Tabachnick, B.; Fidel, L. Using Multivarite Statistics ; Allyn ve Bacon Inc.: Boston, MA, USA, 2001. [ Google Scholar ]
- Taber, K.S. The use of Cronbach’s alpha when developing and reporting research instruments in science education. Res. Sci. Educ. 2018 , 48 , 1273–1296. [ Google Scholar ] [ CrossRef ] [ Green Version ]
- Hair, J.F.; Ringle, C.M.; Sarstedt, M. PLS-SEM: Indeed a silver bullet. J. Mark. Theory Pract. 2011 , 19 , 139–152. [ Google Scholar ] [ CrossRef ]
- Hair, J.F., Jr.; Sarstedt, M.; Hopkins, L.; Kuppelwieser, V.G. Partial least squares structural equation modeling (PLS-SEM): An emerging tool in business research. Eur. Bus. Rev. 2014 , 26 , 106–121. [ Google Scholar ] [ CrossRef ]
- Cronbach, L.J. Coefficient alpha and the internal structure of tests. Psychometrika 1951 , 16 , 297–334. [ Google Scholar ] [ CrossRef ] [ Green Version ]
- Werts, C.E.; Linn, R.L.; Jöreskog, K.G. Intraclass reliability estimates: Testing structural assumptions. Educ. Psychol. Meas. 1974 , 34 , 25–33. [ Google Scholar ] [ CrossRef ]
- Nunnally, B. Psychometric Theory , 3rd ed.; McGraw Hill: New York, NY, USA, 1994. [ Google Scholar ]
- Tarhini, A.; Al-Busaidi, K.A.; Mohammed, A.B.; Maqableh, M. Factors influencing students’ adoption of e-learning: A structural equation modeling approach. J. Int. Educ. Bus. 2017 , 10 , 164–182. [ Google Scholar ] [ CrossRef ]
- Sarstedt, M.; Ringle, C.M.; Hair, J.F. Partial least squares structural equation modeling. In Handbook of Market Research ; Springer: Cham, Switzerland, 2021; pp. 587–632. [ Google Scholar ]
- Götz, O.; Liehr-Gobbers, K.; Krafft, M. Evaluation of structural equation models using the partial least squares (PLS) approach. In Handbook of Partial Least Squares ; Springer: Berlin/Heidelberg, Germany, 2010; pp. 691–711. [ Google Scholar ]
Click here to enlarge figure
| Objective | Analysis | Results | Ref- |
|---|---|---|---|
| by examining the mediation effect of customer satisfaction and loyalty, to develop and validate a conceptual model of value innovation and its impact on firm performance and long-term growth. | The results of the empirical analysis were based on 304 respondents who completed a paper-based survey distributed to Yemeni mobile service providers’ employees using a convenience non-probability sampling technique. | The findings empirically validated the theoretical research model, confirming that value innovation promotes customer satisfaction and loyalty to boost company performance and long-term growth. | [ ] |
| The research aims to find out whether service quality dimensions (tangibility, dependability, responsiveness, empathy, and assurance) predict customer satisfaction after controlling for customer characteristics such as gender, age, and educational level. | Self-administered questionnaires were used to collect primary data. A hierarchical regression analysis was carried out. | Age and education level made no unique contributions to the model, but customers’ gender made a statistically significant negative unique contribution. | [ ] |
| Customer satisfaction, perceived service quality, perceived price fairness, perceived justice in service recovery, and relational bonds are examined in stayers and switchers in the telecom sector. | The PLS-SEM Approach was used to analyze the data. | There are significant differences in the antecedents of loyalty between the two groups (stayers and switchers). | [ ] |
| The goal of this study is to determine customer satisfaction with Asiacell’s prepaid services. | For this study, a questionnaire was administered to 1740 randomly selected customers in various locations throughout SulayManiyah city. | It was discovered that the vast majority of Asiacell users were young customers who were satisfied with the prepaid mobile services provided by the Asiacell company in the city of Sulaymaniyah. | [ ] |
| This study aims to mine Arabic tweets to assess customer satisfaction with a Saudi telecom company. | It was created using a corpus of Arabic tweets and a Python script that searches for real-time tweets that mention Telecom company using hashtags to continuously monitor the latest sentiments of Telecom customers. The machine-classifier and deep learning approach are trained on 20,000 randomly selected tweets from the dataset. | The satisfaction level for each service ranges from 31.50% to 49.25%. One of the proposed solutions is to use 5G to solve the “internet speed” issue, which had the lowest customer satisfaction (31.50%). | [ ] |
| This research aims at how satisfied users are with a customer relationship management (CRM) system in Bahrain. | The data were analyzed using the partial least squares structural equation modeling (PLS-SEM) method. | Employees were highly satisfied with the CRM system, and there was a significant relationship between the selected variables and user satisfaction. | [ ] |
| The research examined whether service quality and customer satisfaction differed depending on which mobile network operator the customer used. | To collect primary data from mobile network users, a self-administered questionnaire was used. The data were analyzed using descriptive and inferential statistics. | The customer’s mobile network operator had a significant impact on service quality and customer satisfaction levels. This study makes an academic contribution by revealing how South African consumers perceive mobile network service providers. | [ ] |
| This study investigates the relationships between customer-perceived expectations, customer-perceived experience, and customer satisfaction in the United Arab Emirates digital telecommunications solution. | The validity of the suggested scales and the research model’s linkages were evaluated and validated using exploratory component analysis and multiple regression analysis. | The research discovered a strong correlation between customer expectation and customer experience, as well as the satisfaction of UAE residents using or engaging with digital telecommunications solutions, regardless of generation. | [ ] |
| The purpose of this project was to assess the impact of technical and functional service quality on customer satisfaction and loyalty. | The collected data was calculated using three Excel software programs (covariance, correlation, and regression analysis). | Customer satisfaction and loyalty are affected by fulfillment and privacy issues. | [ ] |
| To discuss the role of customer engagement in increasing customer loyalty. | A total sample of 798 prepaid and postpaid customers in Thailand were sampled using quota sampling. The t-Test, EFA, CFA, and SEM were used to analyze and test the data. | In terms of online customer engagement, there is a significant difference between prepaid and postpaid customers. | [ ] |
| This study uses a genetic algorithm (GA) to weight service attributes based on survey data to calculate the customer experience management index (CEMI). | Minimizing the difference between calculated CEMI and survey CEMI optimizes attribute weights. | Network coverage, signal strength, and voice quality greatly impact customer satisfaction. | [ ] |
| to investigate the role of consumer characteristics in the influence of customer satisfaction on loyalty in the Indonesian mobile phone service sector. | Utilizing a survey design, 400 respondents were selected using a non-probabilistic random sampling technique, and the obtained data were analyzed using SEM analysis. | The management of a telecommunications company should come up with good marketing plans by coming up with creative and innovative ways to improve service quality, such as using modern, integrated information technology with wide access network coverage to improve signal quality. | [ ] |
| to examine the effect of functional and technological service quality on trust and loyalty in internet services. | The authors have collected data from 300 Internet users residing in various cities in the Iraqi Kurdistan Region. Using structural equation modeling, the data have been evaluated. | Functional quality has less of an impact on loyalty and trust than technical quality. Second, it was found that while functional quality indirectly affects loyalty but not trust, technical quality directly affects both trust and loyalty. | [ ] |
| Objectives | Hypothesis |
|---|---|
| Relationship between customer satisfaction and the factors which impact CS | |
| Measures | Items | Frequency | Percent | Valid Percent | Cumulative Percent | |
|---|---|---|---|---|---|---|
| Valid | Frequency statistics of Gender | Female | 65 | 21.6 | 21.6 | 21.6 |
| Male | 235 | 78.4 | 78.4 | 100 | ||
| Total | 300 | 100 | 100 | |||
| Valid | Frequency Statistics of Age | 15 to 20 | 83 | 27.6 | 27.6 | 27.6 |
| 21 to 25 | 83 | 27.6 | 27.6 | 55.2 | ||
| 26 to 30 | 65 | 21.6 | 21.6 | 76.8 | ||
| 31 to 35 | 41 | 13.6 | 13.6 | 90.4 | ||
| 35 to above | 28 | 9.6 | 9.6 | 100 | ||
| Total | 300 | 100 | 100 | |||
| Valid | Frequency Statistics for Education | Bachelors | 213 | 71 | 71 | 71 |
| Masters | 43 | 14.33 | 14.33 | 85.33 | ||
| PhD | 2 | 0.66 | 0.66 | 86 | ||
| Others | 42 | 14 | 14 | 100 | ||
| Total | 300 | 100 | 100 | 100 | ||
| Valid | Frequency Statistics for Connection | Post-Paid | 132 | 44 | 44 | 44 |
| Pre-Paid | 168 | 56 | 56 | 100 | ||
| Total | 300 | 100 | 100 | |||
| Valid | Frequency Statistics Telecom operator | Mobilink | 104 | 34.66 | 34.66 | 34.66 |
| Telenor | 59 | 19.67 | 19.67 | 54.33 | ||
| U-Fone | 80 | 26.67 | 26.67 | 81.00 | ||
| Zong | 57 | 19.00 | 19 | 100 | ||
| Total | 300 | 100 | 100 | |||
| Valid | Frequency Statistics of Cities using the Internet | Sahiwal | 22 | 7.33 | 7.33 | 7.33 |
| Multan | 166 | 55.33 | 55.33 | 62.66 | ||
| Khanewal | 19 | 6.33 | 6.33 | 68.399 | ||
| Toba Tek Singh | 13 | 4.33 | 4.33 | 73.32 | ||
| Bahawalpur | 30 | 10 | 10 | 83.32 | ||
| Sargodha | 22 | 7.33 | 7.33 | 90.65 | ||
| Other | 28 | 9.35 | 9.35 | 100 | ||
| Total | 300 | 100 | 100 |
| Variables | Number of Items | Cronbach’s Alpha |
|---|---|---|
| Overall | 24 | 0.753 |
| Customer satisfaction | 4 | 0.794 |
| 3G and 4G Network coverage | 5 | 0.512 |
| Customer services | 5 | 0.855 |
| Quality of video calls | 5 | 0.797 |
| Downloading Speed | 5 | 0.74 |
| Variables | Composite Reliability |
|---|---|
| Customer Satisfaction | 0.88 |
| 3G and 4G Network coverage | 0.626 |
| Customer services | 0.9 |
| Quality of video calls | 0.857 |
| Downloading Speed | 0.872 |
| Variables | Cronbach’s Alpha | Composite Reliability | Average Variance Extracted (AVE) |
|---|---|---|---|
| Customer Satisfaction 3G and 4G Network coverage | 0.794 0.512 | 0.88 0.626 | 0.710 0.424 |
| Customer services | 0.855 | 0.9 | 0.694 |
| Quality of video calls | 0.797 | 0.857 | 0.605 |
| Downloading Speed | 0.74 | 0.872 | 0.775 |
| Cronbach’s Alpha | Composite Reliability | Average Variance Extracted (AVE) | |
|---|---|---|---|
| Customer Satisfaction 3G and 4G Network coverage | 0.794 0.512 | 0.88 0.626 | 0.710 0.424 |
| Customer services | 0.855 | 0.9 | 0.694 |
| Quality of video calls | 0.797 | 0.857 | 0.605 |
| Downloading Speed | 0.74 | 0.872 | 0.775 |
| 3G and 4G Network Coverage | Customer Satisfaction | Customer Services | Quality of Video Calls | Downloading Speed | |
|---|---|---|---|---|---|
| CS2 | 0.684 | ||||
| CS3 | 0.922 | ||||
| CS4 | 0.903 | ||||
| CS5 | 0.802 | ||||
| CSF1 | 0.885 | ||||
| CSF2 | 0.87 | ||||
| CSF4 | 0.769 | ||||
| DS3 | 0.795 | ||||
| DS5 | 0.958 | ||||
| NC2 | 0.524 | ||||
| NC3 | 0.196 | ||||
| NC5 | 0.98 | ||||
| QVC2 | 0.861 | ||||
| QVC3 | 0.817 | ||||
| QVC4 | 0.567 | ||||
| QVC5 | 0.83 |
| 3G and 4G Network Coverage | Customer Satisfaction | Customer Services | Quality of Video Calls | Downloading Speed | |
|---|---|---|---|---|---|
| 3G and 4G Network coverage | 0.651 | ||||
| Customer satisfaction | 0.406 | 0.804 | |||
| Customer services | 0.21 | 0.423 | 0.803 | ||
| Quality of video calls | 0.117 | 0.366 | 0.722 | 0.778 | |
| Downloading Speed | 0.197 | 0.3 | 0.853 | 0.717 | 0.8 |
| 3G and 4G Network Coverage | Customer Satisfaction | Customer Services | Quality of Video Calls | Downloading Speed | |
|---|---|---|---|---|---|
| CS2 | 0.171 | 0.167 | 0.684 | 0.622 | 0.734 |
| CS3 | 0.204 | 0.477 | 0.922 | 0.696 | 0.713 |
| CS4 | 0.201 | 0.357 | 0.903 | 0.619 | 0.882 |
| CS5 | 0.121 | 0.299 | 0.802 | 0.497 | 0.572 |
| CSF1 | 0.366 | 0.885 | 0.328 | 0.276 | 0.233 |
| CSF2 | 0.508 | 0.87 | 0.259 | 0.217 | 0.16 |
| CSF4 | 0.125 | 0.769 | 0.5 | 0.449 | 0.383 |
| DS3 | 0.156 | 0.155 | 0.616 | 0.644 | 0.895 |
| DS5 | 0.189 | 0.327 | 0.647 | 0.651 | 0.958 |
| NC2 | 0.524 | 0.101 | 0.153 | 0.158 | 0.06 |
| NC3 | 0.596 | 0.041 | 0.084 | 0.083 | 0.156 |
| NC5 | 0.58 | 0.428 | 0.191 | 0.102 | 0.192 |
| QVC2 | 0.166 | 0.33 | 0.677 | 0.861 | 0.704 |
| QVC3 | 0.147 | 0.197 | 0.581 | 0.817 | 0.607 |
| QVC4 | 0.068 | 0.102 | 0.418 | 0.867 | 0.456 |
| QVC5 | 0.011 | 0.372 | 0.533 | 0.83 | 0.493 |
| Original Sample (O) | Sample Mean (M) | Standard Deviation (STDEV) | T Statistics (|O/STDEV|) | p Values | |
|---|---|---|---|---|---|
| 3G and 4G Network coverage -> Customer Satisfaction | 0.346 | 0.36 | 0.056 | 6.18 | <1% |
| Customer services -> Customer Satisfaction | 0.472 | 0.454 | 0.104 | 4.542 | <1% |
| Quality of video calls -> Customer Satisfaction | 0.221 | 0.224 | 0.076 | 2.913 | <1% |
| Downloading Speed -> Customer Satisfaction | 0.329 | 0.312 | 0.086 | 3.815 | <1% |
| The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
Share and Cite
Haq, I.; Soomro, J.A.; Mazhar, T.; Ullah, I.; Shloul, T.A.; Ghadi, Y.Y.; Ullah, I.; Saad, A.; Tolba, A. Impact of 3G and 4G Technology Performance on Customer Satisfaction in the Telecommunication Industry. Electronics 2023 , 12 , 1697. https://doi.org/10.3390/electronics12071697
Haq I, Soomro JA, Mazhar T, Ullah I, Shloul TA, Ghadi YY, Ullah I, Saad A, Tolba A. Impact of 3G and 4G Technology Performance on Customer Satisfaction in the Telecommunication Industry. Electronics . 2023; 12(7):1697. https://doi.org/10.3390/electronics12071697
Haq, Inayatul, Jahangeer Ahmed Soomro, Tehseen Mazhar, Ikram Ullah, Tamara Al Shloul, Yazeed Yasin Ghadi, Inam Ullah, Aldosary Saad, and Amr Tolba. 2023. "Impact of 3G and 4G Technology Performance on Customer Satisfaction in the Telecommunication Industry" Electronics 12, no. 7: 1697. https://doi.org/10.3390/electronics12071697
Article Metrics
Article access statistics, further information, mdpi initiatives, follow mdpi.

Subscribe to receive issue release notifications and newsletters from MDPI journals
An official website of the United States government
The .gov means it’s official. Federal government websites often end in .gov or .mil. Before sharing sensitive information, make sure you’re on a federal government site.
The site is secure. The https:// ensures that you are connecting to the official website and that any information you provide is encrypted and transmitted securely.
- Publications
- Account settings
Preview improvements coming to the PMC website in October 2024. Learn More or Try it out now .
- Advanced Search
- Journal List
- Sensors (Basel)

Study and Investigation on 5G Technology: A Systematic Review
Ramraj dangi.
1 School of Computing Science and Engineering, VIT University Bhopal, Bhopal 466114, India; [email protected] (R.D.); [email protected] (P.L.)
Praveen Lalwani
Gaurav choudhary.
2 Department of Applied Mathematics and Computer Science, Technical University of Denmark, 2800 Lyngby, Denmark; moc.liamg@7777yrahduohcvaruag
3 Department of Information Security Engineering, Soonchunhyang University, Asan-si 31538, Korea
Giovanni Pau
4 Faculty of Engineering and Architecture, Kore University of Enna, 94100 Enna, Italy; [email protected]
Associated Data
Not applicable.
In wireless communication, Fifth Generation (5G) Technology is a recent generation of mobile networks. In this paper, evaluations in the field of mobile communication technology are presented. In each evolution, multiple challenges were faced that were captured with the help of next-generation mobile networks. Among all the previously existing mobile networks, 5G provides a high-speed internet facility, anytime, anywhere, for everyone. 5G is slightly different due to its novel features such as interconnecting people, controlling devices, objects, and machines. 5G mobile system will bring diverse levels of performance and capability, which will serve as new user experiences and connect new enterprises. Therefore, it is essential to know where the enterprise can utilize the benefits of 5G. In this research article, it was observed that extensive research and analysis unfolds different aspects, namely, millimeter wave (mmWave), massive multiple-input and multiple-output (Massive-MIMO), small cell, mobile edge computing (MEC), beamforming, different antenna technology, etc. This article’s main aim is to highlight some of the most recent enhancements made towards the 5G mobile system and discuss its future research objectives.
1. Introduction
Most recently, in three decades, rapid growth was marked in the field of wireless communication concerning the transition of 1G to 4G [ 1 , 2 ]. The main motto behind this research was the requirements of high bandwidth and very low latency. 5G provides a high data rate, improved quality of service (QoS), low-latency, high coverage, high reliability, and economically affordable services. 5G delivers services categorized into three categories: (1) Extreme mobile broadband (eMBB). It is a nonstandalone architecture that offers high-speed internet connectivity, greater bandwidth, moderate latency, UltraHD streaming videos, virtual reality and augmented reality (AR/VR) media, and many more. (2) Massive machine type communication (eMTC), 3GPP releases it in its 13th specification. It provides long-range and broadband machine-type communication at a very cost-effective price with less power consumption. eMTC brings a high data rate service, low power, extended coverage via less device complexity through mobile carriers for IoT applications. (3) ultra-reliable low latency communication (URLLC) offers low-latency and ultra-high reliability, rich quality of service (QoS), which is not possible with traditional mobile network architecture. URLLC is designed for on-demand real-time interaction such as remote surgery, vehicle to vehicle (V2V) communication, industry 4.0, smart grids, intelligent transport system, etc. [ 3 ].
1.1. Evolution from 1G to 5G
First generation (1G): 1G cell phone was launched between the 1970s and 80s, based on analog technology, which works just like a landline phone. It suffers in various ways, such as poor battery life, voice quality, and dropped calls. In 1G, the maximum achievable speed was 2.4 Kbps.
Second Generation (2G): In 2G, the first digital system was offered in 1991, providing improved mobile voice communication over 1G. In addition, Code-Division Multiple Access (CDMA) and Global System for Mobile (GSM) concepts were also discussed. In 2G, the maximum achievable speed was 1 Mpbs.
Third Generation (3G): When technology ventured from 2G GSM frameworks into 3G universal mobile telecommunication system (UMTS) framework, users encountered higher system speed and quicker download speed making constant video calls. 3G was the first mobile broadband system that was formed to provide the voice with some multimedia. The technology behind 3G was high-speed packet access (HSPA/HSPA+). 3G used MIMO for multiplying the power of the wireless network, and it also used packet switching for fast data transmission.
Fourth Generation (4G): It is purely mobile broadband standard. In digital mobile communication, it was observed information rate that upgraded from 20 to 60 Mbps in 4G [ 4 ]. It works on LTE and WiMAX technologies, as well as provides wider bandwidth up to 100 Mhz. It was launched in 2010.
Fourth Generation LTE-A (4.5G): It is an advanced version of standard 4G LTE. LTE-A uses MIMO technology to combine multiple antennas for both transmitters as well as a receiver. Using MIMO, multiple signals and multiple antennas can work simultaneously, making LTE-A three times faster than standard 4G. LTE-A offered an improved system limit, decreased deferral in the application server, access triple traffic (Data, Voice, and Video) wirelessly at any time anywhere in the world.LTE-A delivers speeds of over 42 Mbps and up to 90 Mbps.
Fifth Generation (5G): 5G is a pillar of digital transformation; it is a real improvement on all the previous mobile generation networks. 5G brings three different services for end user like Extreme mobile broadband (eMBB). It offers high-speed internet connectivity, greater bandwidth, moderate latency, UltraHD streaming videos, virtual reality and augmented reality (AR/VR) media, and many more. Massive machine type communication (eMTC), it provides long-range and broadband machine-type communication at a very cost-effective price with less power consumption. eMTC brings a high data rate service, low power, extended coverage via less device complexity through mobile carriers for IoT applications. Ultra-reliable low latency communication (URLLC) offers low-latency and ultra-high reliability, rich quality of service (QoS), which is not possible with traditional mobile network architecture. URLLC is designed for on-demand real-time interaction such as remote surgery, vehicle to vehicle (V2V) communication, industry 4.0, smart grids, intelligent transport system, etc. 5G faster than 4G and offers remote-controlled operation over a reliable network with zero delays. It provides down-link maximum throughput of up to 20 Gbps. In addition, 5G also supports 4G WWWW (4th Generation World Wide Wireless Web) [ 5 ] and is based on Internet protocol version 6 (IPv6) protocol. 5G provides unlimited internet connection at your convenience, anytime, anywhere with extremely high speed, high throughput, low-latency, higher reliability and scalability, and energy-efficient mobile communication technology [ 6 ]. 5G mainly divided in two parts 6 GHz 5G and Millimeter wave(mmWave) 5G.
6 GHz is a mid frequency band which works as a mid point between capacity and coverage to offer perfect environment for 5G connectivity. 6 GHz spectrum will provide high bandwidth with improved network performance. It offers continuous channels that will reduce the need for network densification when mid-band spectrum is not available and it makes 5G connectivity affordable at anytime, anywhere for everyone.
mmWave is an essential technology of 5G network which build high performance network. 5G mmWave offer diverse services that is why all network providers should add on this technology in their 5G deployment planning. There are lots of service providers who deployed 5G mmWave, and their simulation result shows that 5G mmwave is a far less used spectrum. It provides very high speed wireless communication and it also offers ultra-wide bandwidth for next generation mobile network.
The evolution of wireless mobile technologies are presented in Table 1 . The abbreviations used in this paper are mentioned in Table 2 .
Summary of Mobile Technology.
| Generations | Access Techniques | Transmission Techniques | Error Correction Mechanism | Data Rate | Frequency Band | Bandwidth | Application | Description |
|---|---|---|---|---|---|---|---|---|
| 1G | FDMA, AMPS | Circuit Switching | NA | 2.4 kbps | 800 MHz | Analog | Voice | Let us talk to each other |
| 2G | GSM, TDMA, CDMA | Circuit Switching | NA | 10 kbps | 800 MHz, 900 MHz, 1800 MHz, 1900 MHz | 25 MHz | Voice and Data | Let us send messages and travel with improved data services |
| 3G | WCDMA, UMTS, CDMA 2000, HSUPA/HSDPA | Circuit and Packet Switching | Turbo Codes | 384 kbps to 5 Mbps | 800 MHz, 850 MHz, 900 MHz, 1800 MHz, 1900 MHz, 2100 MHz | 25 MHz | Voice, Data, and Video Calling | Let us experience surfing internet and unleashing mobile applications |
| 4G | LTEA, OFDMA, SCFDMA, WIMAX | Packet switching | Turbo Codes | 100 Mbps to 200 Mbps | 2.3 GHz, 2.5 GHz and 3.5 GHz initially | 100 MHz | Voice, Data, Video Calling, HD Television, and Online Gaming. | Let’s share voice and data over fast broadband internet based on unified networks architectures and IP protocols |
| 5G | BDMA, NOMA, FBMC | Packet Switching | LDPC | 10 Gbps to 50 Gbps | 1.8 GHz, 2.6 GHz and 30–300 GHz | 30–300 GHz | Voice, Data, Video Calling, Ultra HD video, Virtual Reality applications | Expanded the broadband wireless services beyond mobile internet with IOT and V2X. |
Table of Notations and Abbreviations.
| Abbreviation | Full Form | Abbreviation | Full Form |
|---|---|---|---|
| AMF | Access and Mobility Management Function | M2M | Machine-to-Machine |
| AT&T | American Telephone and Telegraph | mmWave | millimeter wave |
| BS | Base Station | NGMN | Next Generation Mobile Networks |
| CDMA | Code-Division Multiple Access | NOMA | Non-Orthogonal Multiple Access |
| CSI | Channel State Information | NFV | Network Functions Virtualization |
| D2D | Device to Device | OFDM | Orthogonal Frequency Division Multiplexing |
| EE | Energy Efficiency | OMA | Orthogonal Multiple Access |
| EMBB | Enhanced mobile broadband: | QoS | Quality of Service |
| ETSI | European Telecommunications Standards Institute | RNN | Recurrent Neural Network |
| eMTC | Massive Machine Type Communication | SDN | Software-Defined Networking |
| FDMA | Frequency Division Multiple Access | SC | Superposition Coding |
| FDD | Frequency Division Duplex | SIC | Successive Interference Cancellation |
| GSM | Global System for Mobile | TDMA | Time Division Multiple Access |
| HSPA | High Speed Packet Access | TDD | Time Division Duplex |
| IoT | Internet of Things | UE | User Equipment |
| IETF | Internet Engineering Task Force | URLLC | Ultra Reliable Low Latency Communication |
| LTE | Long-Term Evolution | UMTC | Universal Mobile Telecommunications System |
| ML | Machine Learning | V2V | Vehicle to Vehicle |
| MIMO | Multiple Input Multiple Output | V2X | Vehicle to Everything |
1.2. Key Contributions
The objective of this survey is to provide a detailed guide of 5G key technologies, methods to researchers, and to help with understanding how the recent works addressed 5G problems and developed solutions to tackle the 5G challenges; i.e., what are new methods that must be applied and how can they solve problems? Highlights of the research article are as follows.
- This survey focused on the recent trends and development in the era of 5G and novel contributions by the researcher community and discussed technical details on essential aspects of the 5G advancement.
- In this paper, the evolution of the mobile network from 1G to 5G is presented. In addition, the growth of mobile communication under different attributes is also discussed.
- This paper covers the emerging applications and research groups working on 5G & different research areas in 5G wireless communication network with a descriptive taxonomy.
- This survey discusses the current vision of the 5G networks, advantages, applications, key technologies, and key features. Furthermore, machine learning prospects are also explored with the emerging requirements in the 5G era. The article also focused on technical aspects of 5G IoT Based approaches and optimization techniques for 5G.
- we provide an extensive overview and recent advancement of emerging technologies of 5G mobile network, namely, MIMO, Non-Orthogonal Multiple Access (NOMA), mmWave, Internet of Things (IoT), Machine Learning (ML), and optimization. Also, a technical summary is discussed by highlighting the context of current approaches and corresponding challenges.
- Security challenges and considerations while developing 5G technology are discussed.
- Finally, the paper concludes with the future directives.
The existing survey focused on architecture, key concepts, and implementation challenges and issues. In contrast, this survey covers the state-of-the-art techniques as well as corresponding recent novel developments by researchers. Various recent significant papers are discussed with the key technologies accelerating the development and production of 5G products.
2. Existing Surveys and Their Applicability
In this paper, a detailed survey on various technologies of 5G networks is presented. Various researchers have worked on different technologies of 5G networks. In this section, Table 3 gives a tabular representation of existing surveys of 5G networks. Massive MIMO, NOMA, small cell, mmWave, beamforming, and MEC are the six main pillars that helped to implement 5G networks in real life.
A comparative overview of existing surveys on different technologies of 5G networks.
| Authors& References | MIMO | NOMA | MmWave | 5G IOT | 5G ML | Small Cell | Beamforming | MEC | 5G Optimization |
|---|---|---|---|---|---|---|---|---|---|
| Chataut and Akl [ ] | Yes | - | Yes | - | - | - | Yes | - | - |
| Prasad et al. [ ] | Yes | - | Yes | - | - | - | - | - | - |
| Kiani and Nsari [ ] | - | Yes | - | - | - | - | - | Yes | - |
| Timotheou and Krikidis [ ] | - | Yes | - | - | - | - | - | - | Yes |
| Yong Niu et al. [ ] | - | - | Yes | - | - | Yes | - | - | - |
| Qiao et al. [ ] | - | - | Yes | - | - | - | - | - | Yes |
| Ramesh et al. [ ] | Yes | - | Yes | - | - | - | - | - | - |
| Khurpade et al. [ ] | Yes | Yes | - | Yes | - | - | - | - | - |
| Bega et al. [ ] | - | - | - | - | Yes | - | - | - | Yes |
| Abrol and jha [ ] | - | - | - | - | - | Yes | - | - | Yes |
| Wei et al. [ ] | - | Yes | - | - | - | - | - | - | |
| Jakob Hoydis et al. [ ] | - | - | - | - | - | Yes | - | - | - |
| Papadopoulos et al. [ ] | Yes | - | - | - | - | - | Yes | - | - |
| Shweta Rajoria et al. [ ] | Yes | - | Yes | - | - | Yes | Yes | - | - |
| Demosthenes Vouyioukas [ ] | Yes | - | - | - | - | - | Yes | - | - |
| Al-Imari et al. [ ] | - | Yes | Yes | - | - | - | - | - | - |
| Michael Till Beck et al. [ ] | - | - | - | - | - | - | Yes | - | |
| Shuo Wang et al. [ ] | - | - | - | - | - | - | Yes | - | |
| Gupta and Jha [ ] | Yes | - | - | - | - | Yes | - | Yes | - |
| Our Survey | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
2.1. Limitations of Existing Surveys
The existing survey focused on architecture, key concepts, and implementation challenges and issues. The numerous current surveys focused on various 5G technologies with different parameters, and the authors did not cover all the technologies of the 5G network in detail with challenges and recent advancements. Few authors worked on MIMO (Non-Orthogonal Multiple Access) NOMA, MEC, small cell technologies. In contrast, some others worked on beamforming, Millimeter-wave (mmWave). But the existing survey did not cover all the technologies of the 5G network from a research and advancement perspective. No detailed survey is available in the market covering all the 5G network technologies and currently published research trade-offs. So, our main aim is to give a detailed study of all the technologies working on the 5G network. In contrast, this survey covers the state-of-the-art techniques as well as corresponding recent novel developments by researchers. Various recent significant papers are discussed with the key technologies accelerating the development and production of 5G products. This survey article collected key information about 5G technology and recent advancements, and it can be a kind of a guide for the reader. This survey provides an umbrella approach to bring multiple solutions and recent improvements in a single place to accelerate the 5G research with the latest key enabling solutions and reviews. A systematic layout representation of the survey in Figure 1 . We provide a state-of-the-art comparative overview of the existing surveys on different technologies of 5G networks in Table 3 .

Systematic layout representation of survey.
2.2. Article Organization
This article is organized under the following sections. Section 2 presents existing surveys and their applicability. In Section 3 , the preliminaries of 5G technology are presented. In Section 4 , recent advances of 5G technology based on Massive MIMO, NOMA, Millimeter Wave, 5G with IoT, machine learning for 5G, and Optimization in 5G are provided. In Section 5 , a description of novel 5G features over 4G is provided. Section 6 covered all the security concerns of the 5G network. Section 7 , 5G technology based on above-stated challenges summarize in tabular form. Finally, Section 8 and Section 9 conclude the study, which paves the path for future research.
3. Preliminary Section
3.1. emerging 5g paradigms and its features.
5G provides very high speed, low latency, and highly salable connectivity between multiple devices and IoT worldwide. 5G will provide a very flexible model to develop a modern generation of applications and industry goals [ 26 , 27 ]. There are many services offered by 5G network architecture are stated below:
Massive machine to machine communications: 5G offers novel, massive machine-to-machine communications [ 28 ], also known as the IoT [ 29 ], that provide connectivity between lots of machines without any involvement of humans. This service enhances the applications of 5G and provides connectivity between agriculture, construction, and industries [ 30 ].
Ultra-reliable low latency communications (URLLC): This service offers real-time management of machines, high-speed vehicle-to-vehicle connectivity, industrial connectivity and security principles, and highly secure transport system, and multiple autonomous actions. Low latency communications also clear up a different area where remote medical care, procedures, and operation are all achievable [ 31 ].
Enhanced mobile broadband: Enhance mobile broadband is an important use case of 5G system, which uses massive MIMO antenna, mmWave, beamforming techniques to offer very high-speed connectivity across a wide range of areas [ 32 ].
For communities: 5G provides a very flexible internet connection between lots of machines to make smart homes, smart schools, smart laboratories, safer and smart automobiles, and good health care centers [ 33 ].
For businesses and industry: As 5G works on higher spectrum ranges from 24 to 100 GHz. This higher frequency range provides secure low latency communication and high-speed wireless connectivity between IoT devices and industry 4.0, which opens a market for end-users to enhance their business models [ 34 ].
New and Emerging technologies: As 5G came up with many new technologies like beamforming, massive MIMO, mmWave, small cell, NOMA, MEC, and network slicing, it introduced many new features to the market. Like virtual reality (VR), users can experience the physical presence of people who are millions of kilometers away from them. Many new technologies like smart homes, smart workplaces, smart schools, smart sports academy also came into the market with this 5G Mobile network model [ 35 ].
3.2. Commercial Service Providers of 5G
5G provides high-speed internet browsing, streaming, and downloading with very high reliability and low latency. 5G network will change your working style, and it will increase new business opportunities and provide innovations that we cannot imagine. This section covers top service providers of 5G network [ 36 , 37 ].
Ericsson: Ericsson is a Swedish multinational networking and telecommunications company, investing around 25.62 billion USD in 5G network, which makes it the biggest telecommunication company. It claims that it is the only company working on all the continents to make the 5G network a global standard for the next generation wireless communication. Ericsson developed the first 5G radio prototype that enables the operators to set up the live field trials in their network, which helps operators understand how 5G reacts. It plays a vital role in the development of 5G hardware. It currently provides 5G services in over 27 countries with content providers like China Mobile, GCI, LGU+, AT&T, Rogers, and many more. It has 100 commercial agreements with different operators as of 2020.
Verizon: It is American multinational telecommunication which was founded in 1983. Verizon started offering 5G services in April 2020, and by December 2020, it has actively provided 5G services in 30 cities of the USA. They planned that by the end of 2021, they would deploy 5G in 30 more new cities. Verizon deployed a 5G network on mmWave, a very high band spectrum between 30 to 300 GHz. As it is a significantly less used spectrum, it provides very high-speed wireless communication. MmWave offers ultra-wide bandwidth for next-generation mobile networks. MmWave is a faster and high-band spectrum that has a limited range. Verizon planned to increase its number of 5G cells by 500% by 2020. Verizon also has an ultra wide-band flagship 5G service which is the best 5G service that increases the market price of Verizon.
Nokia: Nokia is a Finnish multinational telecommunications company which was founded in 1865. Nokia is one of the companies which adopted 5G technology very early. It is developing, researching, and building partnerships with various 5G renders to offer 5G communication as soon as possible. Nokia collaborated with Deutsche Telekom and Hamburg Port Authority and provided them 8000-hectare site for their 5G MoNArch project. Nokia is the only company that supplies 5G technology to all the operators of different countries like AT&T, Sprint, T-Mobile US and Verizon in the USA, Korea Telecom, LG U+ and SK Telecom in South Korea and NTT DOCOMO, KDDI, and SoftBank in Japan. Presently, Nokia has around 150+ agreements and 29 live networks all over the world. Nokia is continuously working hard on 5G technology to expand 5G networks all over the globe.
AT&T: AT&T is an American multinational company that was the first to deploy a 5G network in reality in 2018. They built a gigabit 5G network connection in Waco, TX, Kalamazoo, MI, and South Bend to achieve this. It is the first company that archives 1–2 gigabit per second speed in 2019. AT&T claims that it provides a 5G network connection among 225 million people worldwide by using a 6 GHz spectrum band.
T-Mobile: T-Mobile US (TMUS) is an American wireless network operator which was the first service provider that offers a real 5G nationwide network. The company knew that high-band 5G was not feasible nationwide, so they used a 600 MHz spectrum to build a significant portion of its 5G network. TMUS is planning that by 2024 they will double the total capacity and triple the full 5G capacity of T-Mobile and Sprint combined. The sprint buyout is helping T-Mobile move forward the company’s current market price to 129.98 USD.
Samsung: Samsung started their research in 5G technology in 2011. In 2013, Samsung successfully developed the world’s first adaptive array transceiver technology operating in the millimeter-wave Ka bands for cellular communications. Samsung provides several hundred times faster data transmission than standard 4G for core 5G mobile communication systems. The company achieved a lot of success in the next generation of technology, and it is considered one of the leading companies in the 5G domain.
Qualcomm: Qualcomm is an American multinational corporation in San Diego, California. It is also one of the leading company which is working on 5G chip. Qualcomm’s first 5G modem chip was announced in October 2016, and a prototype was demonstrated in October 2017. Qualcomm mainly focuses on building products while other companies talk about 5G; Qualcomm is building the technologies. According to one magazine, Qualcomm was working on three main areas of 5G networks. Firstly, radios that would use bandwidth from any network it has access to; secondly, creating more extensive ranges of spectrum by combining smaller pieces; and thirdly, a set of services for internet applications.
ZTE Corporation: ZTE Corporation was founded in 1985. It is a partially Chinese state-owned technology company that works in telecommunication. It was a leading company that worked on 4G LTE, and it is still maintaining its value and doing research and tests on 5G. It is the first company that proposed Pre5G technology with some series of solutions.
NEC Corporation: NEC Corporation is a Japanese multinational information technology and electronics corporation headquartered in Minato, Tokyo. ZTE also started their research on 5G, and they introduced a new business concept. NEC’s main aim is to develop 5G NR for the global mobile system and create secure and intelligent technologies to realize 5G services.
Cisco: Cisco is a USA networking hardware company that also sleeves up for 5G network. Cisco’s primary focus is to support 5G in three ways: Service—enable 5G services faster so all service providers can increase their business. Infrastructure—build 5G-oriented infrastructure to implement 5G more quickly. Automation—make a more scalable, flexible, and reliable 5G network. The companies know the importance of 5G, and they want to connect more than 30 billion devices in the next couple of years. Cisco intends to work on network hardening as it is a vital part of 5G network. Cisco used AI with deep learning to develop a 5G Security Architecture, enabling Secure Network Transformation.
3.3. 5G Research Groups
Many research groups from all over the world are working on a 5G wireless mobile network [ 38 ]. These groups are continuously working on various aspects of 5G. The list of those research groups are presented as follows: 5GNOW (5th Generation Non-Orthogonal Waveform for Asynchronous Signaling), NEWCOM (Network of Excellence in Wireless Communication), 5GIC (5G Innovation Center), NYU (New York University) Wireless, 5GPPP (5G Infrastructure Public-Private Partnership), EMPHATIC (Enhanced Multi-carrier Technology for Professional Adhoc and Cell-Based Communication), ETRI(Electronics and Telecommunication Research Institute), METIS (Mobile and wireless communication Enablers for the Twenty-twenty Information Society) [ 39 ]. The various research groups along with the research area are presented in Table 4 .
Research groups working on 5G mobile networks.
| Research Groups | Research Area | Description |
|---|---|---|
| METIS (Mobile and wireless communications Enablers for Twenty-twenty (2020) Information Society) | Working 5G Framework | METIS focused on RAN architecture and designed an air interface which evaluates data rates on peak hours, traffic load per region, traffic volume per user and actual client data rates. They have generate METIS published an article on February, 2015 in which they developed RAN architecture with simulation results. They design an air interface which evaluates data rates on peak hours, traffic load per region, traffic volume per user and actual client data rates.They have generate very less RAN latency under 1ms. They also introduced diverse RAN model and traffic flow in different situation like malls, offices, colleges and stadiums. |
| 5G PPP (5G Infrastructure Public Private Partnership) | Next generation mobile network communication, high speed Connectivity. | Fifth generation infrastructure public partnership project is a joint startup by two groups (European Commission and European ICT industry). 5G-PPP will provide various standards architectures, solutions and technologies for next generation mobile network in coming decade. The main motto behind 5G-PPP is that, through this project, European Commission wants to give their contribution in smart cities, e-health, intelligent transport, education, entertainment, and media. |
| 5GNOW (5th Generation Non-Orthogonal Waveforms for asynchronous signaling) | Non-orthogonal Multiple Access | 5GNOW’s is working on modulation and multiplexing techniques for next generation network. 5GNOW’s offers ultra-high reliability and ultra-low latency communication with visible waveform for 5G. 5GNOW’s also worked on acquiring time and frequency plane information of a signal using short term Fourier transform (STFT) |
| EMPhAtiC (Enhanced Multicarrier Technology for Professional Ad-Hoc and Cell-Based Communications) | MIMO Transmission | EMPhAtiC is working on MIMO transmission to develop a secure communication techniques with asynchronicity based on flexible filter bank and multihop. Recently they also launched MIMO based trans-receiver technique under frequency selective channels for Filter Bank Multi-Carrier (FBMC) |
| NEWCOM (Network of Excellence in Wireless Communications) | Advanced aspects of wireless communications | NEWCOM is working on energy efficiency, channel efficiency, multihop communication in wireless communication. Recently, they are working on cloud RAN, mobile broadband, local and distributed antenna techniques and multi-hop communication for 5G network. Finally, in their final research they give on result that QAM modulation schema, system bandwidth and resource block is used to process the base band. |
| NYU New York University Wireless | Millimeter Wave | NYU Wireless is research center working on wireless communication, sensors, networking and devices. In their recent research, NYU focuses on developing smaller and lighter antennas with directional beamforming to provide reliable wireless communication. |
| 5GIC 5G Innovation Centre | Decreasing network costs, Preallocation of resources according to user’s need, point-to-point communication, Highspeed connectivity. | 5GIC, is a UK’s research group, which is working on high-speed wireless communication. In their recent research they got 1Tbps speed in point-to-point wireless communication. Their main focus is on developing ultra-low latency app services. |
| ETRI (Electronics and Telecommunication Research Institute) | Device-to-device communication, MHN protocol stack | ETRI (Electronics and Telecommunication Research Institute), is a research group of Korea, which is focusing on improving the reliability of 5G network, device-to-device communication and MHN protocol stack. |
3.4. 5G Applications
5G is faster than 4G and offers remote-controlled operation over a reliable network with zero delays. It provides down-link maximum throughput of up to 20 Gbps. In addition, 5G also supports 4G WWWW (4th Generation World Wide Wireless Web) [ 5 ] and is based on Internet protocol version 6 (IPv6) protocol. 5G provides unlimited internet connection at your convenience, anytime, anywhere with extremely high speed, high throughput, low-latency, higher reliability, greater scalablility, and energy-efficient mobile communication technology [ 6 ].
There are lots of applications of 5G mobile network are as follows:
- High-speed mobile network: 5G is an advancement on all the previous mobile network technologies, which offers very high speed downloading speeds 0 of up to 10 to 20 Gbps. The 5G wireless network works as a fiber optic internet connection. 5G is different from all the conventional mobile transmission technologies, and it offers both voice and high-speed data connectivity efficiently. 5G offers very low latency communication of less than a millisecond, useful for autonomous driving and mission-critical applications. 5G will use millimeter waves for data transmission, providing higher bandwidth and a massive data rate than lower LTE bands. As 5 Gis a fast mobile network technology, it will enable virtual access to high processing power and secure and safe access to cloud services and enterprise applications. Small cell is one of the best features of 5G, which brings lots of advantages like high coverage, high-speed data transfer, power saving, easy and fast cloud access, etc. [ 40 ].
- Entertainment and multimedia: In one analysis in 2015, it was found that more than 50 percent of mobile internet traffic was used for video downloading. This trend will surely increase in the future, which will make video streaming more common. 5G will offer High-speed streaming of 4K videos with crystal clear audio, and it will make a high definition virtual world on your mobile. 5G will benefit the entertainment industry as it offers 120 frames per second with high resolution and higher dynamic range video streaming, and HD TV channels can also be accessed on mobile devices without any interruptions. 5G provides low latency high definition communication so augmented reality (AR), and virtual reality (VR) will be very easily implemented in the future. Virtual reality games are trendy these days, and many companies are investing in HD virtual reality games. The 5G network will offer high-speed internet connectivity with a better gaming experience [ 41 ].
- Smart homes : smart home appliances and products are in demand these days. The 5G network makes smart homes more real as it offers high-speed connectivity and monitoring of smart appliances. Smart home appliances are easily accessed and configured from remote locations using the 5G network as it offers very high-speed low latency communication.
- Smart cities: 5G wireless network also helps develop smart cities applications such as automatic traffic management, weather update, local area broadcasting, energy-saving, efficient power supply, smart lighting system, water resource management, crowd management, emergency control, etc.
- Industrial IoT: 5G wireless technology will provide lots of features for future industries such as safety, process tracking, smart packing, shipping, energy efficiency, automation of equipment, predictive maintenance, and logistics. 5G smart sensor technology also offers smarter, safer, cost-effective, and energy-saving industrial IoT operations.
- Smart Farming: 5G technology will play a crucial role in agriculture and smart farming. 5G sensors and GPS technology will help farmers track live attacks on crops and manage them quickly. These smart sensors can also be used for irrigation, pest, insect, and electricity control.
- Autonomous Driving: The 5G wireless network offers very low latency high-speed communication, significant for autonomous driving. It means self-driving cars will come to real life soon with 5G wireless networks. Using 5G autonomous cars can easily communicate with smart traffic signs, objects, and other vehicles running on the road. 5G’s low latency feature makes self-driving more real as every millisecond is essential for autonomous vehicles, decision-making is done in microseconds to avoid accidents.
- Healthcare and mission-critical applications: 5G technology will bring modernization in medicine where doctors and practitioners can perform advanced medical procedures. The 5G network will provide connectivity between all classrooms, so attending seminars and lectures will be easier. Through 5G technology, patients can connect with doctors and take their advice. Scientists are building smart medical devices which can help people with chronic medical conditions. The 5G network will boost the healthcare industry with smart devices, the internet of medical things, smart sensors, HD medical imaging technologies, and smart analytics systems. 5G will help access cloud storage, so accessing healthcare data will be very easy from any location worldwide. Doctors and medical practitioners can easily store and share large files like MRI reports within seconds using the 5G network.
- Satellite Internet: In many remote areas, ground base stations are not available, so 5G will play a crucial role in providing connectivity in such areas. The 5G network will provide connectivity using satellite systems, and the satellite system uses a constellation of multiple small satellites to provide connectivity in urban and rural areas across the world.
4. 5G Technologies
This section describes recent advances of 5G Massive MIMO, 5G NOMA, 5G millimeter wave, 5G IOT, 5G with machine learning, and 5G optimization-based approaches. In addition, the summary is also presented in each subsection that paves the researchers for the future research direction.

4.1. 5G Massive MIMO
Multiple-input-multiple-out (MIMO) is a very important technology for wireless systems. It is used for sending and receiving multiple signals simultaneously over the same radio channel. MIMO plays a very big role in WI-FI, 3G, 4G, and 4G LTE-A networks. MIMO is mainly used to achieve high spectral efficiency and energy efficiency but it was not up to the mark MIMO provides low throughput and very low reliable connectivity. To resolve this, lots of MIMO technology like single user MIMO (SU-MIMO), multiuser MIMO (MU-MIMO) and network MIMO were used. However, these new MIMO also did not still fulfill the demand of end users. Massive MIMO is an advancement of MIMO technology used in the 5G network in which hundreds and thousands of antennas are attached with base stations to increase throughput and spectral efficiency. Multiple transmit and receive antennas are used in massive MIMO to increase the transmission rate and spectral efficiency. When multiple UEs generate downlink traffic simultaneously, massive MIMO gains higher capacity. Massive MIMO uses extra antennas to move energy into smaller regions of space to increase spectral efficiency and throughput [ 43 ]. In traditional systems data collection from smart sensors is a complex task as it increases latency, reduced data rate and reduced reliability. While massive MIMO with beamforming and huge multiplexing techniques can sense data from different sensors with low latency, high data rate and higher reliability. Massive MIMO will help in transmitting the data in real-time collected from different sensors to central monitoring locations for smart sensor applications like self-driving cars, healthcare centers, smart grids, smart cities, smart highways, smart homes, and smart enterprises [ 44 ].
Highlights of 5G Massive MIMO technology are as follows:
- Data rate: Massive MIMO is advised as the one of the dominant technologies to provide wireless high speed and high data rate in the gigabits per seconds.
- The relationship between wave frequency and antenna size: Both are inversely proportional to each other. It means lower frequency signals need a bigger antenna and vise versa.

Pictorial representation of multi-input and multi-output (MIMO).
- MIMO role in 5G: Massive MIMO will play a crucial role in the deployment of future 5G mobile communication as greater spectral and energy efficiency could be enabled.
State-of-the-Art Approaches
Plenty of approaches were proposed to resolve the issues of conventional MIMO [ 7 ].
The MIMO multirate, feed-forward controller is suggested by Mae et al. [ 46 ]. In the simulation, the proposed model generates the smooth control input, unlike the conventional MIMO, which generates oscillated control inputs. It also outperformed concerning the error rate. However, a combination of multirate and single rate can be used for better results.
The performance of stand-alone MIMO, distributed MIMO with and without corporation MIMO, was investigated by Panzner et al. [ 47 ]. In addition, an idea about the integration of large scale in the 5G technology was also presented. In the experimental analysis, different MIMO configurations are considered. The variation in the ratio of overall transmit antennas to spatial is deemed step-wise from equality to ten.
The simulation of massive MIMO noncooperative and cooperative systems for down-link behavior was performed by He et al. [ 48 ]. It depends on present LTE systems, which deal with various antennas in the base station set-up. It was observed that collaboration in different BS improves the system behaviors, whereas throughput is reduced slightly in this approach. However, a new method can be developed which can enhance both system behavior and throughput.
In [ 8 ], different approaches that increased the energy efficiency benefits provided by massive MIMO were presented. They analyzed the massive MIMO technology and described the detailed design of the energy consumption model for massive MIMO systems. This article has explored several techniques to enhance massive MIMO systems’ energy efficiency (EE) gains. This paper reviews standard EE-maximization approaches for the conventional massive MIMO systems, namely, scaling number of antennas, real-time implementing low-complexity operations at the base station (BS), power amplifier losses minimization, and radio frequency (RF) chain minimization requirements. In addition, open research direction is also identified.
In [ 49 ], various existing approaches based on different antenna selection and scheduling, user selection and scheduling, and joint antenna and user scheduling methods adopted in massive MIMO systems are presented in this paper. The objective of this survey article was to make awareness about the current research and future research direction in MIMO for systems. They analyzed that complete utilization of resources and bandwidth was the most crucial factor which enhances the sum rate.
In [ 50 ], authors discussed the development of various techniques for pilot contamination. To calculate the impact of pilot contamination in time division duplex (TDD) massive MIMO system, TDD and frequency division duplexing FDD patterns in massive MIMO techniques are used. They discussed different issues in pilot contamination in TDD massive MIMO systems with all the possible future directions of research. They also classified various techniques to generate the channel information for both pilot-based and subspace-based approaches.
In [ 19 ], the authors defined the uplink and downlink services for a massive MIMO system. In addition, it maintains a performance matrix that measures the impact of pilot contamination on different performances. They also examined the various application of massive MIMO such as small cells, orthogonal frequency-division multiplexing (OFDM) schemes, massive MIMO IEEE 802, 3rd generation partnership project (3GPP) specifications, and higher frequency bands. They considered their research work crucial for cutting edge massive MIMO and covered many issues like system throughput performance and channel state acquisition at higher frequencies.
In [ 13 ], various approaches were suggested for MIMO future generation wireless communication. They made a comparative study based on performance indicators such as peak data rate, energy efficiency, latency, throughput, etc. The key findings of this survey are as follows: (1) spatial multiplexing improves the energy efficiency; (2) design of MIMO play a vital role in the enhancement of throughput; (3) enhancement of mMIMO focusing on energy & spectral performance; (4) discussed the future challenges to improve the system design.
In [ 51 ], the study of large-scale MIMO systems for an energy-efficient system sharing method was presented. For the resource allocation, circuit energy and transmit energy expenditures were taken into consideration. In addition, the optimization techniques were applied for an energy-efficient resource sharing system to enlarge the energy efficiency for individual QoS and energy constraints. The author also examined the BS configuration, which includes homogeneous and heterogeneous UEs. While simulating, they discussed that the total number of transmit antennas plays a vital role in boosting energy efficiency. They highlighted that the highest energy efficiency was obtained when the BS was set up with 100 antennas that serve 20 UEs.
This section includes various works done on 5G MIMO technology by different author’s. Table 5 shows how different author’s worked on improvement of various parameters such as throughput, latency, energy efficiency, and spectral efficiency with 5G MIMO technology.
Summary of massive MIMO-based approaches in 5G technology.
| Approach | Throughput | Latency | Energy Efficiency | Spectral Efficiency |
|---|---|---|---|---|
| Panzner et al. [ ] | Good | Low | Good | Average |
| He et al. [ ] | Average | Low | Average | - |
| Prasad et al. [ ] | Good | - | Good | Avearge |
| Papadopoulos et al. [ ] | Good | Low | Average | Avearge |
| Ramesh et al. [ ] | Good | Average | Good | Good |
| Zhou et al. [ ] | Average | - | Good | Average |
4.2. 5G Non-Orthogonal Multiple Access (NOMA)
NOMA is a very important radio access technology used in next generation wireless communication. Compared to previous orthogonal multiple access techniques, NOMA offers lots of benefits like high spectrum efficiency, low latency with high reliability and high speed massive connectivity. NOMA mainly works on a baseline to serve multiple users with the same resources in terms of time, space and frequency. NOMA is mainly divided into two main categories one is code domain NOMA and another is power domain NOMA. Code-domain NOMA can improve the spectral efficiency of mMIMO, which improves the connectivity in 5G wireless communication. Code-domain NOMA was divided into some more multiple access techniques like sparse code multiple access, lattice-partition multiple access, multi-user shared access and pattern-division multiple access [ 52 ]. Power-domain NOMA is widely used in 5G wireless networks as it performs well with various wireless communication techniques such as MIMO, beamforming, space-time coding, network coding, full-duplex and cooperative communication etc. [ 53 ]. The conventional orthogonal frequency-division multiple access (OFDMA) used by 3GPP in 4G LTE network provides very low spectral efficiency when bandwidth resources are allocated to users with low channel state information (CSI). NOMA resolved this issue as it enables users to access all the subcarrier channels so bandwidth resources allocated to the users with low CSI can still be accessed by the users with strong CSI which increases the spectral efficiency. The 5G network will support heterogeneous architecture in which small cell and macro base stations work for spectrum sharing. NOMA is a key technology of the 5G wireless system which is very helpful for heterogeneous networks as multiple users can share their data in a small cell using the NOMA principle.The NOMA is helpful in various applications like ultra-dense networks (UDN), machine to machine (M2M) communication and massive machine type communication (mMTC). As NOMA provides lots of features it has some challenges too such as NOMA needs huge computational power for a large number of users at high data rates to run the SIC algorithms. Second, when users are moving from the networks, to manage power allocation optimization is a challenging task for NOMA [ 54 ]. Hybrid NOMA (HNOMA) is a combination of power-domain and code-domain NOMA. HNOMA uses both power differences and orthogonal resources for transmission among multiple users. As HNOMA is using both power-domain NOMA and code-domain NOMA it can achieve higher spectral efficiency than Power-domain NOMA and code-domain NOMA. In HNOMA multiple groups can simultaneously transmit signals at the same time. It uses a message passing algorithm (MPA) and successive interference cancellation (SIC)-based detection at the base station for these groups [ 55 ].
Highlights of 5G NOMA technology as follows:

Pictorial representation of orthogonal and Non-Orthogonal Multiple Access (NOMA).
- NOMA provides higher data rates and resolves all the loop holes of OMA that makes 5G mobile network more scalable and reliable.
- As multiple users use same frequency band simultaneously it increases the performance of whole network.
- To setup intracell and intercell interference NOMA provides nonorthogonal transmission on the transmitter end.
- The primary fundamental of NOMA is to improve the spectrum efficiency by strengthening the ramification of receiver.
State-of-the-Art of Approaches
A plenty of approaches were developed to address the various issues in NOMA.
A novel approach to address the multiple receiving signals at the same frequency is proposed in [ 22 ]. In NOMA, multiple users use the same sub-carrier, which improves the fairness and throughput of the system. As a nonorthogonal method is used among multiple users, at the time of retrieving the user’s signal at the receiver’s end, joint processing is required. They proposed solutions to optimize the receiver and the radio resource allocation of uplink NOMA. Firstly, the authors proposed an iterative MUDD which utilizes the information produced by the channel decoder to improve the performance of the multiuser detector. After that, the author suggested a power allocation and novel subcarrier that enhances the users’ weighted sum rate for the NOMA scheme. Their proposed model showed that NOMA performed well as compared to OFDM in terms of fairness and efficiency.
In [ 53 ], the author’s reviewed a power-domain NOMA that uses superposition coding (SC) and successive interference cancellation (SIC) at the transmitter and the receiver end. Lots of analyses were held that described that NOMA effectively satisfies user data rate demands and network-level of 5G technologies. The paper presented a complete review of recent advances in the 5G NOMA system. It showed the comparative analysis regarding allocation procedures, user fairness, state-of-the-art efficiency evaluation, user pairing pattern, etc. The study also analyzes NOMA’s behavior when working with other wireless communication techniques, namely, beamforming, MIMO, cooperative connections, network, space-time coding, etc.
In [ 9 ], the authors proposed NOMA with MEC, which improves the QoS as well as reduces the latency of the 5G wireless network. This model increases the uplink NOMA by decreasing the user’s uplink energy consumption. They formulated an optimized NOMA framework that reduces the energy consumption of MEC by using computing and communication resource allocation, user clustering, and transmit powers.
In [ 10 ], the authors proposed a model which investigates outage probability under average channel state information CSI and data rate in full CSI to resolve the problem of optimal power allocation, which increase the NOMA downlink system among users. They developed simple low-complexity algorithms to provide the optimal solution. The obtained simulation results showed NOMA’s efficiency, achieving higher performance fairness compared to the TDMA configurations. It was observed from the results that NOMA, through the appropriate power amplifiers (PA), ensures the high-performance fairness requirement for the future 5G wireless communication networks.
In [ 56 ], researchers discussed that the NOMA technology and waveform modulation techniques had been used in the 5G mobile network. Therefore, this research gave a detailed survey of non-orthogonal waveform modulation techniques and NOMA schemes for next-generation mobile networks. By analyzing and comparing multiple access technologies, they considered the future evolution of these technologies for 5G mobile communication.
In [ 57 ], the authors surveyed non-orthogonal multiple access (NOMA) from the development phase to the recent developments. They have also compared NOMA techniques with traditional OMA techniques concerning information theory. The author discussed the NOMA schemes categorically as power and code domain, including the design principles, operating principles, and features. Comparison is based upon the system’s performance, spectral efficiency, and the receiver’s complexity. Also discussed are the future challenges, open issues, and their expectations of NOMA and how it will support the key requirements of 5G mobile communication systems with massive connectivity and low latency.
In [ 17 ], authors present the first review of an elementary NOMA model with two users, which clarify its central precepts. After that, a general design with multicarrier supports with a random number of users on each sub-carrier is analyzed. In performance evaluation with the existing approaches, resource sharing and multiple-input multiple-output NOMA are examined. Furthermore, they took the key elements of NOMA and its potential research demands. Finally, they reviewed the two-user SC-NOMA design and a multi-user MC-NOMA design to highlight NOMA’s basic approaches and conventions. They also present the research study about the performance examination, resource assignment, and MIMO in NOMA.
In this section, various works by different authors done on 5G NOMA technology is covered. Table 6 shows how other authors worked on the improvement of various parameters such as spectral efficiency, fairness, and computing capacity with 5G NOMA technology.
Summary of NOMA-based approaches in 5G technology.
| Approach | Spectral Efficiency | Fairness | Computing Capacity |
|---|---|---|---|
| Al-Imari et al. [ ] | Good | Good | Average |
| Islam et al. [ ] | Good | Average | Average |
| Kiani and Nsari [ ] | Average | Good | Good |
| Timotheou and Krikidis [ ] | Good | Good | Average |
| Wei et al. [ ] | Good | Average | Good |
4.3. 5G Millimeter Wave (mmWave)
Millimeter wave is an extremely high frequency band, which is very useful for 5G wireless networks. MmWave uses 30 GHz to 300 GHz spectrum band for transmission. The frequency band between 30 GHz to 300 GHz is known as mmWave because these waves have wavelengths between 1 to 10 mm. Till now radar systems and satellites are only using mmWave as these are very fast frequency bands which provide very high speed wireless communication. Many mobile network providers also started mmWave for transmitting data between base stations. Using two ways the speed of data transmission can be improved one is by increasing spectrum utilization and second is by increasing spectrum bandwidth. Out of these two approaches increasing bandwidth is quite easy and better. The frequency band below 5 GHz is very crowded as many technologies are using it so to boost up the data transmission rate 5G wireless network uses mmWave technology which instead of increasing spectrum utilization, increases the spectrum bandwidth [ 58 ]. To maximize the signal bandwidth in wireless communication the carrier frequency should also be increased by 5% because the signal bandwidth is directly proportional to carrier frequencies. The frequency band between 28 GHz to 60 GHz is very useful for 5G wireless communication as 28 GHz frequency band offers up to 1 GHz spectrum bandwidth and 60 GHz frequency band offers 2 GHz spectrum bandwidth. 4G LTE provides 2 GHz carrier frequency which offers only 100 MHz spectrum bandwidth. However, the use of mmWave increases the spectrum bandwidth 10 times, which leads to better transmission speeds [ 59 , 60 ].
Highlights of 5G mmWave are as follows:

Pictorial representation of millimeter wave.
- The 5G mmWave offer three advantages: (1) MmWave is very less used new Band, (2) MmWave signals carry more data than lower frequency wave, and (3) MmWave can be incorporated with MIMO antenna with the potential to offer a higher magnitude capacity compared to current communication systems.
In [ 11 ], the authors presented the survey of mmWave communications for 5G. The advantage of mmWave communications is adaptability, i.e., it supports the architectures and protocols up-gradation, which consists of integrated circuits, systems, etc. The authors over-viewed the present solutions and examined them concerning effectiveness, performance, and complexity. They also discussed the open research issues of mmWave communications in 5G concerning the software-defined network (SDN) architecture, network state information, efficient regulation techniques, and the heterogeneous system.
In [ 61 ], the authors present the recent work done by investigators in 5G; they discussed the design issues and demands of mmWave 5G antennas for cellular handsets. After that, they designed a small size and low-profile 60 GHz array of antenna units that contain 3D planer mesh-grid antenna elements. For the future prospect, a framework is designed in which antenna components are used to operate cellular handsets on mmWave 5G smartphones. In addition, they cross-checked the mesh-grid array of antennas with the polarized beam for upcoming hardware challenges.
In [ 12 ], the authors considered the suitability of the mmWave band for 5G cellular systems. They suggested a resource allocation system for concurrent D2D communications in mmWave 5G cellular systems, and it improves network efficiency and maintains network connectivity. This research article can serve as guidance for simulating D2D communications in mmWave 5G cellular systems. Massive mmWave BS may be set up to obtain a high delivery rate and aggregate efficiency. Therefore, many wireless users can hand off frequently between the mmWave base terminals, and it emerges the demand to search the neighbor having better network connectivity.
In [ 62 ], the authors provided a brief description of the cellular spectrum which ranges from 1 GHz to 3 GHz and is very crowed. In addition, they presented various noteworthy factors to set up mmWave communications in 5G, namely, channel characteristics regarding mmWave signal attenuation due to free space propagation, atmospheric gaseous, and rain. In addition, hybrid beamforming architecture in the mmWave technique is analyzed. They also suggested methods for the blockage effect in mmWave communications due to penetration damage. Finally, the authors have studied designing the mmWave transmission with small beams in nonorthogonal device-to-device communication.
This section covered various works done on 5G mmWave technology. The Table 7 shows how different author’s worked on the improvement of various parameters i.e., transmission rate, coverage, and cost, with 5G mmWave technology.
Summary of existing mmWave-based approaches in 5G technology.
| Approach | Transmission Rate | Coverage | Cost |
|---|---|---|---|
| Hong et al. [ ] | Average | Average | Low |
| Qiao et al. [ ] | Average | Good | Average |
| Wei et al. [ ] | Good | Average | Low |
4.4. 5G IoT Based Approaches
The 5G mobile network plays a big role in developing the Internet of Things (IoT). IoT will connect lots of things with the internet like appliances, sensors, devices, objects, and applications. These applications will collect lots of data from different devices and sensors. 5G will provide very high speed internet connectivity for data collection, transmission, control, and processing. 5G is a flexible network with unused spectrum availability and it offers very low cost deployment that is why it is the most efficient technology for IoT [ 63 ]. In many areas, 5G provides benefits to IoT, and below are some examples:
Smart homes: smart home appliances and products are in demand these days. The 5G network makes smart homes more real as it offers high speed connectivity and monitoring of smart appliances. Smart home appliances are easily accessed and configured from remote locations using the 5G network, as it offers very high speed low latency communication.
Smart cities: 5G wireless network also helps in developing smart cities applications such as automatic traffic management, weather update, local area broadcasting, energy saving, efficient power supply, smart lighting system, water resource management, crowd management, emergency control, etc.
Industrial IoT: 5G wireless technology will provide lots of features for future industries such as safety, process tracking, smart packing, shipping, energy efficiency, automation of equipment, predictive maintenance and logistics. 5G smart sensor technology also offers smarter, safer, cost effective, and energy-saving industrial operation for industrial IoT.
Smart Farming: 5G technology will play a crucial role for agriculture and smart farming. 5G sensors and GPS technology will help farmers to track live attacks on crops and manage them quickly. These smart sensors can also be used for irrigation control, pest control, insect control, and electricity control.
Autonomous Driving: 5G wireless network offers very low latency high speed communication which is very significant for autonomous driving. It means self-driving cars will come to real life soon with 5G wireless networks. Using 5G autonomous cars can easily communicate with smart traffic signs, objects and other vehicles running on the road. 5G’s low latency feature makes self-driving more real as every millisecond is important for autonomous vehicles, decision taking is performed in microseconds to avoid accidents [ 64 ].
Highlights of 5G IoT are as follows:

Pictorial representation of IoT with 5G.
- 5G with IoT is a new feature of next-generation mobile communication, which provides a high-speed internet connection between moderated devices. 5G IoT also offers smart homes, smart devices, sensors, smart transportation systems, smart industries, etc., for end-users to make them smarter.
- IoT deals with moderate devices which connect through the internet. The approach of the IoT has made the consideration of the research associated with the outcome of providing wearable, smart-phones, sensors, smart transportation systems, smart devices, washing machines, tablets, etc., and these diverse systems are associated to a common interface with the intelligence to connect.
- Significant IoT applications include private healthcare systems, traffic management, industrial management, and tactile internet, etc.
Plenty of approaches is devised to address the issues of IoT [ 14 , 65 , 66 ].
In [ 65 ], the paper focuses on 5G mobile systems due to the emerging trends and developing technologies, which results in the exponential traffic growth in IoT. The author surveyed the challenges and demands during deployment of the massive IoT applications with the main focus on mobile networking. The author reviewed the features of standard IoT infrastructure, along with the cellular-based, low-power wide-area technologies (LPWA) such as eMTC, extended coverage (EC)-GSM-IoT, as well as noncellular, low-power wide-area (LPWA) technologies such as SigFox, LoRa etc.
In [ 14 ], the authors presented how 5G technology copes with the various issues of IoT today. It provides a brief review of existing and forming 5G architectures. The survey indicates the role of 5G in the foundation of the IoT ecosystem. IoT and 5G can easily combine with improved wireless technologies to set up the same ecosystem that can fulfill the current requirement for IoT devices. 5G can alter nature and will help to expand the development of IoT devices. As the process of 5G unfolds, global associations will find essentials for setting up a cross-industry engagement in determining and enlarging the 5G system.
In [ 66 ], the author introduced an IoT authentication scheme in a 5G network, with more excellent reliability and dynamic. The scheme proposed a privacy-protected procedure for selecting slices; it provided an additional fog node for proper data transmission and service types of the subscribers, along with service-oriented authentication and key understanding to maintain the secrecy, precision of users, and confidentiality of service factors. Users anonymously identify the IoT servers and develop a vital channel for service accessibility and data cached on local fog nodes and remote IoT servers. The author performed a simulation to manifest the security and privacy preservation of the user over the network.
This section covered various works done on 5G IoT by multiple authors. Table 8 shows how different author’s worked on the improvement of numerous parameters, i.e., data rate, security requirement, and performance with 5G IoT.
Summary of IoT-based approaches in 5G technology.
| Approach | Data Rate | Security Requirement | Performance |
|---|---|---|---|
| Akpakwu et al. [ ] | Good | Average | Good |
| Khurpade et al. [ ] | Average | - | Average |
| Ni et al. [ ] | Good | Average | Average |
4.5. Machine Learning Techniques for 5G
Various machine learning (ML) techniques were applied in 5G networks and mobile communication. It provides a solution to multiple complex problems, which requires a lot of hand-tuning. ML techniques can be broadly classified as supervised, unsupervised, and reinforcement learning. Let’s discuss each learning technique separately and where it impacts the 5G network.
Supervised Learning, where user works with labeled data; some 5G network problems can be further categorized as classification and regression problems. Some regression problems such as scheduling nodes in 5G and energy availability can be predicted using Linear Regression (LR) algorithm. To accurately predict the bandwidth and frequency allocation Statistical Logistic Regression (SLR) is applied. Some supervised classifiers are applied to predict the network demand and allocate network resources based on the connectivity performance; it signifies the topology setup and bit rates. Support Vector Machine (SVM) and NN-based approximation algorithms are used for channel learning based on observable channel state information. Deep Neural Network (DNN) is also employed to extract solutions for predicting beamforming vectors at the BS’s by taking mapping functions and uplink pilot signals into considerations.
In unsupervised Learning, where the user works with unlabeled data, various clustering techniques are applied to enhance network performance and connectivity without interruptions. K-means clustering reduces the data travel by storing data centers content into clusters. It optimizes the handover estimation based on mobility pattern and selection of relay nodes in the V2V network. Hierarchical clustering reduces network failure by detecting the intrusion in the mobile wireless network; unsupervised soft clustering helps in reducing latency by clustering fog nodes. The nonparametric Bayesian unsupervised learning technique reduces traffic in the network by actively serving the user’s requests and demands. Other unsupervised learning techniques such as Adversarial Auto Encoders (AAE) and Affinity Propagation Clustering techniques detect irregular behavior in the wireless spectrum and manage resources for ultradense small cells, respectively.
In case of an uncertain environment in the 5G wireless network, reinforcement learning (RL) techniques are employed to solve some problems. Actor-critic reinforcement learning is used for user scheduling and resource allocation in the network. Markov decision process (MDP) and Partially Observable MDP (POMDP) is used for Quality of Experience (QoE)-based handover decision-making for Hetnets. Controls packet call admission in HetNets and channel access process for secondary users in a Cognitive Radio Network (CRN). Deep RL is applied to decide the communication channel and mobility and speeds up the secondary user’s learning rate using an antijamming strategy. Deep RL is employed in various 5G network application parameters such as resource allocation and security [ 67 ]. Table 9 shows the state-of-the-art ML-based solution for 5G network.
The state-of-the-art ML-based solution for 5G network.
| Author References | Key Contribution | ML Applied | Network Participants Component | 5G Network Application Parameter | |||||
|---|---|---|---|---|---|---|---|---|---|
| Alave et al. [ ] | Network traffic prediction | LSTM and DNN | ✓ | ✓ | * | ✓ | ✓ | ✓ | X |
| Bega et al. [ ] | Network slice admission control algorithm | Machine Learning and Deep Learing | ✓ | X | X | ✓ | ✓ | ✓ | X |
| Suomalainen et al. [ ] | 5G Security | Machine Learning | X | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| Bashir et al. [ ] | Resource Allocation | Machine Learning | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | X |
| Balevi et al. [ ] | Low Latency communication | Unsupervised clustering | X | ✓ | X | ✓ | ✓ | ✓ | X |
| Tayyaba et al. [ ] | Resource Management | LSTM, CNN, and DNN | ✓ | ✓ | X | ✓ | ✓ | ✓ | ✓ |
| Sim et al. [ ] | 5G mmWave Vehicular communication | FML (Fast machine Learning) | X | ✓ | * | ✓ | ✓ | ✓ | X |
| Li et al. [ ] | Intrusion Detection System | Machine Learning | X | ✓ | X | ✓ | ✓ | ✓ | ✓ |
| Kafle et al. [ ] | 5G Network Slicing | Machine Learning | X | ✓ | X | ✓ | ✓ | ✓ | ✓ |
| Chen et al. [ ] | Physical-Layer Channel Authentication | Machine Learning | X | ✓ | X | X | X | X | ✓ |
| Sevgican et al. [ ] | Intelligent Network Data Analytics Function in 5G | Machine Learning | ✓ | X | ✓ | X | X | * | * |
| Abidi et al. [ ] | Optimal 5G network slicing | Machine Learning and Deep Learing | X | ✓ | X | ✓ | ✓ | ✓ | * |
Highlights of machine learning techniques for 5G are as follows:

Pictorial representation of machine learning (ML) in 5G.
- In ML, a model will be defined which fulfills the desired requirements through which desired results are obtained. In the later stage, it examines accuracy from obtained results.
- ML plays a vital role in 5G network analysis for threat detection, network load prediction, final arrangement, and network formation. Searching for a better balance between power, length of antennas, area, and network thickness crossed with the spontaneous use of services in the universe of individual users and types of devices.
In [ 79 ], author’s firstly describes the demands for the traditional authentication procedures and benefits of intelligent authentication. The intelligent authentication method was established to improve security practice in 5G-and-beyond wireless communication systems. Thereafter, the machine learning paradigms for intelligent authentication were organized into parametric and non-parametric research methods, as well as supervised, unsupervised, and reinforcement learning approaches. As a outcome, machine learning techniques provide a new paradigm into authentication under diverse network conditions and unstable dynamics. In addition, prompt intelligence to the security management to obtain cost-effective, better reliable, model-free, continuous, and situation-aware authentication.
In [ 68 ], the authors proposed a machine learning-based model to predict the traffic load at a particular location. They used a mobile network traffic dataset to train a model that can calculate the total number of user requests at a time. To launch access and mobility management function (AMF) instances according to the requirement as there were no predictions of user request the performance automatically degrade as AMF does not handle these requests at a time. Earlier threshold-based techniques were used to predict the traffic load, but that approach took too much time; therefore, the authors proposed RNN algorithm-based ML to predict the traffic load, which gives efficient results.
In [ 15 ], authors discussed the issue of network slice admission, resource allocation among subscribers, and how to maximize the profit of infrastructure providers. The author proposed a network slice admission control algorithm based on SMDP (decision-making process) that guarantees the subscribers’ best acceptance policies and satisfiability (tenants). They also suggested novel N3AC, a neural network-based algorithm that optimizes performance under various configurations, significantly outperforms practical and straightforward approaches.
This section includes various works done on 5G ML by different authors. Table 10 shows the state-of-the-art work on the improvement of various parameters such as energy efficiency, Quality of Services (QoS), and latency with 5G ML.
The state-of-the-art ML-based approaches in 5G technology.
| Approach | Energy Efficiency | Quality of Services (QoS) | Latency |
|---|---|---|---|
| Fang et al. [ ] | Good | Good | Average |
| Alawe et al. [ ] | Good | Average | Low |
| Bega et al. [ ] | - | Good | Average |
4.6. Optimization Techniques for 5G
Optimization techniques may be applied to capture NP-Complete or NP-Hard problems in 5G technology. This section briefly describes various research works suggested for 5G technology based on optimization techniques.
In [ 80 ], Massive MIMO technology is used in 5G mobile network to make it more flexible and scalable. The MIMO implementation in 5G needs a significant number of radio frequencies is required in the RF circuit that increases the cost and energy consumption of the 5G network. This paper provides a solution that increases the cost efficiency and energy efficiency with many radio frequency chains for a 5G wireless communication network. They give an optimized energy efficient technique for MIMO antenna and mmWave technologies based 5G mobile communication network. The proposed Energy Efficient Hybrid Precoding (EEHP) algorithm to increase the energy efficiency for the 5G wireless network. This algorithm minimizes the cost of an RF circuit with a large number of RF chains.
In [ 16 ], authors have discussed the growing demand for energy efficiency in the next-generation networks. In the last decade, they have figured out the things in wireless transmissions, which proved a change towards pursuing green communication for the next generation system. The importance of adopting the correct EE metric was also reviewed. Further, they worked through the different approaches that can be applied in the future for increasing the network’s energy and posed a summary of the work that was completed previously to enhance the energy productivity of the network using these capabilities. A system design for EE development using relay selection was also characterized, along with an observation of distinct algorithms applied for EE in relay-based ecosystems.
In [ 81 ], authors presented how AI-based approach is used to the setup of Self Organizing Network (SON) functionalities for radio access network (RAN) design and optimization. They used a machine learning approach to predict the results for 5G SON functionalities. Firstly, the input was taken from various sources; then, prediction and clustering-based machine learning models were applied to produce the results. Multiple AI-based devices were used to extract the knowledge analysis to execute SON functionalities smoothly. Based on results, they tested how self-optimization, self-testing, and self-designing are done for SON. The author also describes how the proposed mechanism classifies in different orders.
In [ 82 ], investigators examined the working of OFDM in various channel environments. They also figured out the changes in frame duration of the 5G TDD frame design. Subcarrier spacing is beneficial to obtain a small frame length with control overhead. They provided various techniques to reduce the growing guard period (GP) and cyclic prefix (CP) like complete utilization of multiple subcarrier spacing, management and data parts of frame at receiver end, various uses of timing advance (TA) or total control of flexible CP size.
This section includes various works that were done on 5G optimization by different authors. Table 11 shows how other authors worked on the improvement of multiple parameters such as energy efficiency, power optimization, and latency with 5G optimization.
Summary of Optimization Based Approaches in 5G Technology.
| Approach | Energy Efficiency | Power Optimization | Latency |
|---|---|---|---|
| Zi et al. [ ] | Good | - | Average |
| Abrol and jha [ ] | Good | Good | - |
| Pérez-Romero et al. [ ] | - | Average | Average |
| Lähetkangas et al. [ ] | Average | - | Low |
5. Description of Novel 5G Features over 4G
This section presents descriptions of various novel features of 5G, namely, the concept of small cell, beamforming, and MEC.
5.1. Small Cell
Small cells are low-powered cellular radio access nodes which work in the range of 10 meters to a few kilometers. Small cells play a very important role in implementation of the 5G wireless network. Small cells are low power base stations which cover small areas. Small cells are quite similar with all the previous cells used in various wireless networks. However, these cells have some advantages like they can work with low power and they are also capable of working with high data rates. Small cells help in rollout of 5G network with ultra high speed and low latency communication. Small cells in the 5G network use some new technologies like MIMO, beamforming, and mmWave for high speed data transmission. The design of small cells hardware is very simple so its implementation is quite easier and faster. There are three types of small cell tower available in the market. Femtocells, picocells, and microcells [ 83 ]. As shown in the Table 12 .
Types of Small cells.
| Types of Small Cell | Coverage Radius | Indoor Outdoor | Transmit Power | Number of Users | Backhaul Type | Cost |
|---|---|---|---|---|---|---|
| Femtocells | 30–165 ft 10–50 m | Indoor | 100 mW 20 dBm | 8–16 | Wired, fiber | Low |
| Picocells | 330–820 ft 100–250 m | Indoor Outdoor | 250 mW 24 dBm | 32–64 | Wired, fiber | Low |
| Microcells | 1600–8000 ft 500–250 m | Outdoor | 2000–500 mW 32–37 dBm | 200 | Wired, fiber, Microwave | Medium |
MmWave is a very high band spectrum between 30 to 300 GHz. As it is a significantly less used spectrum, it provides very high-speed wireless communication. MmWave offers ultra-wide bandwidth for next-generation mobile networks. MmWave has lots of advantages, but it has some disadvantages, too, such as mmWave signals are very high-frequency signals, so they have more collision with obstacles in the air which cause the signals loses energy quickly. Buildings and trees also block MmWave signals, so these signals cover a shorter distance. To resolve these issues, multiple small cell stations are installed to cover the gap between end-user and base station [ 18 ]. Small cell covers a very shorter range, so the installation of a small cell depends on the population of a particular area. Generally, in a populated place, the distance between each small cell varies from 10 to 90 meters. In the survey [ 20 ], various authors implemented small cells with massive MIMO simultaneously. They also reviewed multiple technologies used in 5G like beamforming, small cell, massive MIMO, NOMA, device to device (D2D) communication. Various problems like interference management, spectral efficiency, resource management, energy efficiency, and backhauling are discussed. The author also gave a detailed presentation of all the issues occurring while implementing small cells with various 5G technologies. As shown in the Figure 7 , mmWave has a higher range, so it can be easily blocked by the obstacles as shown in Figure 7 a. This is one of the key concerns of millimeter-wave signal transmission. To solve this issue, the small cell can be placed at a short distance to transmit the signals easily, as shown in Figure 7 b.

Pictorial representation of communication with and without small cells.
5.2. Beamforming
Beamforming is a key technology of wireless networks which transmits the signals in a directional manner. 5G beamforming making a strong wireless connection toward a receiving end. In conventional systems when small cells are not using beamforming, moving signals to particular areas is quite difficult. Beamforming counter this issue using beamforming small cells are able to transmit the signals in particular direction towards a device like mobile phone, laptops, autonomous vehicle and IoT devices. Beamforming is improving the efficiency and saves the energy of the 5G network. Beamforming is broadly divided into three categories: Digital beamforming, analog beamforming and hybrid beamforming. Digital beamforming: multiuser MIMO is equal to digital beamforming which is mainly used in LTE Advanced Pro and in 5G NR. In digital beamforming the same frequency or time resources can be used to transmit the data to multiple users at the same time which improves the cell capacity of wireless networks. Analog Beamforming: In mmWave frequency range 5G NR analog beamforming is a very important approach which improves the coverage. In digital beamforming there are chances of high pathloss in mmWave as only one beam per set of antenna is formed. While the analog beamforming saves high pathloss in mmWave. Hybrid beamforming: hybrid beamforming is a combination of both analog beamforming and digital beamforming. In the implementation of MmWave in 5G network hybrid beamforming will be used [ 84 ].
Wireless signals in the 4G network are spreading in large areas, and nature is not Omnidirectional. Thus, energy depletes rapidly, and users who are accessing these signals also face interference problems. The beamforming technique is used in the 5G network to resolve this issue. In beamforming signals are directional. They move like a laser beam from the base station to the user, so signals seem to be traveling in an invisible cable. Beamforming helps achieve a faster data rate; as the signals are directional, it leads to less energy consumption and less interference. In [ 21 ], investigators evolve some techniques which reduce interference and increase system efficiency of the 5G mobile network. In this survey article, the authors covered various challenges faced while designing an optimized beamforming algorithm. Mainly focused on different design parameters such as performance evaluation and power consumption. In addition, they also described various issues related to beamforming like CSI, computation complexity, and antenna correlation. They also covered various research to cover how beamforming helps implement MIMO in next-generation mobile networks [ 85 ]. Figure 8 shows the pictorial representation of communication with and without using beamforming.

Pictorial Representation of communication with and without using beamforming.
5.3. Mobile Edge Computing
Mobile Edge Computing (MEC) [ 24 ]: MEC is an extended version of cloud computing that brings cloud resources closer to the end-user. When we talk about computing, the very first thing that comes to our mind is cloud computing. Cloud computing is a very famous technology that offers many services to end-user. Still, cloud computing has many drawbacks. The services available in the cloud are too far from end-users that create latency, and cloud user needs to download the complete application before use, which also increases the burden to the device [ 86 ]. MEC creates an edge between the end-user and cloud server, bringing cloud computing closer to the end-user. Now, all the services, namely, video conferencing, virtual software, etc., are offered by this edge that improves cloud computing performance. Another essential feature of MEC is that the application is split into two parts, which, first one is available at cloud server, and the second is at the user’s device. Therefore, the user need not download the complete application on his device that increases the performance of the end user’s device. Furthermore, MEC provides cloud services at very low latency and less bandwidth. In [ 23 , 87 ], the author’s investigation proved that successful deployment of MEC in 5G network increases the overall performance of 5G architecture. Graphical differentiation between cloud computing and mobile edge computing is presented in Figure 9 .

Pictorial representation of cloud computing vs. mobile edge computing.
6. 5G Security
Security is the key feature in the telecommunication network industry, which is necessary at various layers, to handle 5G network security in applications such as IoT, Digital forensics, IDS and many more [ 88 , 89 ]. The authors [ 90 ], discussed the background of 5G and its security concerns, challenges and future directions. The author also introduced the blockchain technology that can be incorporated with the IoT to overcome the challenges in IoT. The paper aims to create a security framework which can be incorporated with the LTE advanced network, and effective in terms of cost, deployment and QoS. In [ 91 ], author surveyed various form of attacks, the security challenges, security solutions with respect to the affected technology such as SDN, Network function virtualization (NFV), Mobile Clouds and MEC, and security standardizations of 5G, i.e., 3GPP, 5GPPP, Internet Engineering Task Force (IETF), Next Generation Mobile Networks (NGMN), European Telecommunications Standards Institute (ETSI). In [ 92 ], author elaborated various technological aspects, security issues and their existing solutions and also mentioned the new emerging technological paradigms for 5G security such as blockchain, quantum cryptography, AI, SDN, CPS, MEC, D2D. The author aims to create new security frameworks for 5G for further use of this technology in development of smart cities, transportation and healthcare. In [ 93 ], author analyzed the threats and dark threat, security aspects concerned with SDN and NFV, also their Commercial & Industrial Security Corporation (CISCO) 5G vision and new security innovations with respect to the new evolving architectures of 5G [ 94 ].
AuthenticationThe identification of the user in any network is made with the help of authentication. The different mobile network generations from 1G to 5G have used multiple techniques for user authentication. 5G utilizes the 5G Authentication and Key Agreement (AKA) authentication method, which shares a cryptographic key between user equipment (UE) and its home network and establishes a mutual authentication process between the both [ 95 ].
Access Control To restrict the accessibility in the network, 5G supports access control mechanisms to provide a secure and safe environment to the users and is controlled by network providers. 5G uses simple public key infrastructure (PKI) certificates for authenticating access in the 5G network. PKI put forward a secure and dynamic environment for the 5G network. The simple PKI technique provides flexibility to the 5G network; it can scale up and scale down as per the user traffic in the network [ 96 , 97 ].
Communication Security 5G deals to provide high data bandwidth, low latency, and better signal coverage. Therefore secure communication is the key concern in the 5G network. UE, mobile operators, core network, and access networks are the main focal point for the attackers in 5G communication. Some of the common attacks in communication at various segments are Botnet, message insertion, micro-cell, distributed denial of service (DDoS), and transport layer security (TLS)/secure sockets layer (SSL) attacks [ 98 , 99 ].
Encryption The confidentiality of the user and the network is done using encryption techniques. As 5G offers multiple services, end-to-end (E2E) encryption is the most suitable technique applied over various segments in the 5G network. Encryption forbids unauthorized access to the network and maintains the data privacy of the user. To encrypt the radio traffic at Packet Data Convergence Protocol (PDCP) layer, three 128-bits keys are applied at the user plane, nonaccess stratum (NAS), and access stratum (AS) [ 100 ].
7. Summary of 5G Technology Based on Above-Stated Challenges
In this section, various issues addressed by investigators in 5G technologies are presented in Table 13 . In addition, different parameters are considered, such as throughput, latency, energy efficiency, data rate, spectral efficiency, fairness & computing capacity, transmission rate, coverage, cost, security requirement, performance, QoS, power optimization, etc., indexed from R1 to R14.
Summary of 5G Technology above stated challenges (R1:Throughput, R2:Latency, R3:Energy Efficiency, R4:Data Rate, R5:Spectral efficiency, R6:Fairness & Computing Capacity, R7:Transmission Rate, R8:Coverage, R9:Cost, R10:Security requirement, R11:Performance, R12:Quality of Services (QoS), R13:Power Optimization).
| Approach | R1 | R2 | R3 | R4 | R5 | R6 | R7 | R8 | R9 | R10 | R11 | R12 | R13 | R14 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Panzner et al. [ ] | Good | Low | Good | - | Avg | - | - | - | - | - | - | - | - | - |
| Qiao et al. [ ] | - | - | - | - | - | - | - | Avg | Good | Avg | - | - | - | - |
| He et al. [ ] | Avg | Low | Avg | - | - | - | - | - | - | - | - | - | - | - |
| Abrol and jha [ ] | - | - | Good | - | - | - | - | - | - | - | - | - | - | Good |
| Al-Imari et al. [ ] | - | - | - | - | Good | Good | Avg | - | - | - | - | - | - | - |
| Papadopoulos et al. [ ] | Good | Low | Avg | - | Avg | - | - | - | - | - | - | - | - | - |
| Kiani and Nsari [ ] | - | - | - | - | Avg | Good | Good | - | - | - | - | - | - | - |
| Beck [ ] | - | Low | - | - | - | - | - | Avg | - | - | - | Good | - | Avg |
| Ni et al. [ ] | - | - | - | Good | - | - | - | - | - | - | Avg | Avg | - | - |
| Elijah [ ] | Avg | Low | Avg | - | - | - | - | - | - | - | - | - | - | - |
| Alawe et al. [ ] | - | Low | Good | - | - | - | - | - | - | - | - | - | Avg | - |
| Zhou et al. [ ] | Avg | - | Good | - | Avg | - | - | - | - | - | - | - | - | - |
| Islam et al. [ ] | - | - | - | - | Good | Avg | Avg | - | - | - | - | - | - | - |
| Bega et al. [ ] | - | Avg | - | - | - | - | - | - | - | - | - | - | Good | - |
| Akpakwu et al. [ ] | - | - | - | Good | - | - | - | - | - | - | Avg | Good | - | - |
| Wei et al. [ ] | - | - | - | - | - | - | - | Good | Avg | Low | - | - | - | - |
| Khurpade et al. [ ] | - | - | - | Avg | - | - | - | - | - | - | - | Avg | - | - |
| Timotheou and Krikidis [ ] | - | - | - | - | Good | Good | Avg | - | - | - | - | - | - | - |
| Wang [ ] | Avg | Low | Avg | Avg | - | - | - | - | - | - | - | - | - | - |
| Akhil Gupta & R. K. Jha [ ] | - | - | Good | Avg | Good | - | - | - | - | - | - | Good | Good | - |
| Pérez-Romero et al. [ ] | - | - | Avg | - | - | - | - | - | - | - | - | - | - | Avg |
| Pi [ ] | - | - | - | - | - | - | - | Good | Good | Avg | - | - | - | - |
| Zi et al. [ ] | - | Avg | Good | - | - | - | - | - | - | - | - | - | - | - |
| Chin [ ] | - | - | Good | Avg | - | - | - | - | - | Avg | - | Good | - | - |
| Mamta Agiwal [ ] | - | Avg | - | Good | - | - | - | - | - | - | Good | Avg | - | - |
| Ramesh et al. [ ] | Good | Avg | Good | - | Good | - | - | - | - | - | - | - | - | - |
| Niu [ ] | - | - | - | - | - | - | - | Good | Avg | Avg | - | - | - | |
| Fang et al. [ ] | - | Avg | Good | - | - | - | - | - | - | - | - | - | Good | - |
| Hoydis [ ] | - | - | Good | - | Good | - | - | - | - | Avg | - | Good | - | - |
| Wei et al. [ ] | - | - | - | - | Good | Avg | Good | - | - | - | - | - | - | - |
| Hong et al. [ ] | - | - | - | - | - | - | - | - | Avg | Avg | Low | - | - | - |
| Rashid [ ] | - | - | - | Good | - | - | - | Good | - | - | - | Avg | - | Good |
| Prasad et al. [ ] | Good | - | Good | - | Avg | - | - | - | - | - | - | - | - | - |
| Lähetkangas et al. [ ] | - | Low | Av | - | - | - | - | - | - | - | - | - | - | - |
8. Conclusions
This survey article illustrates the emergence of 5G, its evolution from 1G to 5G mobile network, applications, different research groups, their work, and the key features of 5G. It is not just a mobile broadband network, different from all the previous mobile network generations; it offers services like IoT, V2X, and Industry 4.0. This paper covers a detailed survey from multiple authors on different technologies in 5G, such as massive MIMO, Non-Orthogonal Multiple Access (NOMA), millimeter wave, small cell, MEC (Mobile Edge Computing), beamforming, optimization, and machine learning in 5G. After each section, a tabular comparison covers all the state-of-the-research held in these technologies. This survey also shows the importance of these newly added technologies and building a flexible, scalable, and reliable 5G network.
9. Future Findings
This article covers a detailed survey on the 5G mobile network and its features. These features make 5G more reliable, scalable, efficient at affordable rates. As discussed in the above sections, numerous technical challenges originate while implementing those features or providing services over a 5G mobile network. So, for future research directions, the research community can overcome these challenges while implementing these technologies (MIMO, NOMA, small cell, mmWave, beam-forming, MEC) over a 5G network. 5G communication will bring new improvements over the existing systems. Still, the current solutions cannot fulfill the autonomous system and future intelligence engineering requirements after a decade. There is no matter of discussion that 5G will provide better QoS and new features than 4G. But there is always room for improvement as the considerable growth of centralized data and autonomous industry 5G wireless networks will not be capable of fulfilling their demands in the future. So, we need to move on new wireless network technology that is named 6G. 6G wireless network will bring new heights in mobile generations, as it includes (i) massive human-to-machine communication, (ii) ubiquitous connectivity between the local device and cloud server, (iii) creation of data fusion technology for various mixed reality experiences and multiverps maps. (iv) Focus on sensing and actuation to control the network of the entire world. The 6G mobile network will offer new services with some other technologies; these services are 3D mapping, reality devices, smart homes, smart wearable, autonomous vehicles, artificial intelligence, and sense. It is expected that 6G will provide ultra-long-range communication with a very low latency of 1 ms. The per-user bit rate in a 6G wireless network will be approximately 1 Tbps, and it will also provide wireless communication, which is 1000 times faster than 5G networks.
Acknowledgments
Author contributions.
Conceptualization: R.D., I.Y., G.C., P.L. data gathering: R.D., G.C., P.L, I.Y. funding acquisition: I.Y. investigation: I.Y., G.C., G.P. methodology: R.D., I.Y., G.C., P.L., G.P., survey: I.Y., G.C., P.L, G.P., R.D. supervision: G.C., I.Y., G.P. validation: I.Y., G.P. visualization: R.D., I.Y., G.C., P.L. writing, original draft: R.D., I.Y., G.C., P.L., G.P. writing, review, and editing: I.Y., G.C., G.P. All authors have read and agreed to the published version of the manuscript.
This paper was supported by Soonchunhyang University.
Institutional Review Board Statement
Informed consent statement, data availability statement, conflicts of interest.
The authors declare no conflict of interest.
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Data analysis with ASU SKYSURF team earns high school student first published research paper
SKYSURF is the largest Hubble Space Telescope archive program to date. Courtesy image
High school students who are pursuing a degree in a STEM field usually focus on their coursework and SATs with the hope of getting accepted into a top research university. Once in college, they typically join research groups to apply their knowledge and publish their results in peer-reviewed journals.
Purvansh Bhatia, a recent graduate of BASIS Scottsdale , has already accomplished an impressive feat by having a research paper published. He is the lead author of a paper recently published in the American Astronomical Society journal .
“I'm elated that two years of my research with SKYSURF has produced this paper, and joining the group as a 10th grader, I never imagined that I would come this far,” Bhatia said. “I couldn't have done any of it without Dr. Timothy Carleton , who mentored me from an uninitiated student to an astronomical academic. Sincere thanks to him, Professor Windhorst, and everyone else who contributed to this paper.”
This achievement is particularly notable because it's the first time Rogier Windhorst , a Regents Professor in ASU’s School of Earth and Space Exploration , has had a high school student in his group conducting data analysis — let alone publish the findings as a first author of a refereed journal.
Bhatia collaborated with members of the SKYSURF research group, including research scientist Rolf Jansen , assistant research scientist Tim Carleton, and graduate associate Rosalia O’Brien , all from the School of Earth and Space Exploration.
“Purvansh Bahtia is one of those ultra-bright high school students from the BASIS school system, who did research in our group and got it published as lead author,” Windhorst said. “He found that the Sloan Digital Sky survey can predict which of our many thousands of Hubble SKYSURF images was affected by the bias of the observer who selected the Hubble target.”
As Bhatia’s high school chapter comes to a close, his recent publication achievement marks the beginning of his next chapter and promises a bright future in the field of STEM research as he embarks on his college career this fall.
More Science and technology

Setting new standards for materials testing
In sunny parts of the world, solar panels seem to be everywhere. The panels, typically made from silicon, provide an electricity source that produces no carbon emissions. While they are an important…

ASU program gives graduate students firsthand look at science policy in nation's capital
For international students like Jide Olugbade, going to Washington, D.C., was a dream come true: He could get an insider’s view of the city's movers and shakers and everything in between. Thanks to…

ASU study points to origin of cumulative culture in human evolution
Each of us individually is the accumulated product of thousands of generations that have come before us in an unbroken line. Our culture and technology today are also the result of thousands of years…
Suggestions or feedback?
MIT News | Massachusetts Institute of Technology
- Machine learning
- Social justice
- Black holes
- Classes and programs
Departments
- Aeronautics and Astronautics
- Brain and Cognitive Sciences
- Architecture
- Political Science
- Mechanical Engineering
Centers, Labs, & Programs
- Abdul Latif Jameel Poverty Action Lab (J-PAL)
- Picower Institute for Learning and Memory
- Lincoln Laboratory
- School of Architecture + Planning
- School of Engineering
- School of Humanities, Arts, and Social Sciences
- Sloan School of Management
- School of Science
- MIT Schwarzman College of Computing
A technique for more effective multipurpose robots
Press contact :, media download.
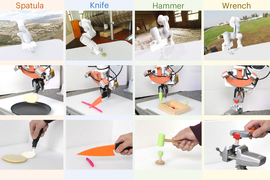
*Terms of Use:
Images for download on the MIT News office website are made available to non-commercial entities, press and the general public under a Creative Commons Attribution Non-Commercial No Derivatives license . You may not alter the images provided, other than to crop them to size. A credit line must be used when reproducing images; if one is not provided below, credit the images to "MIT."
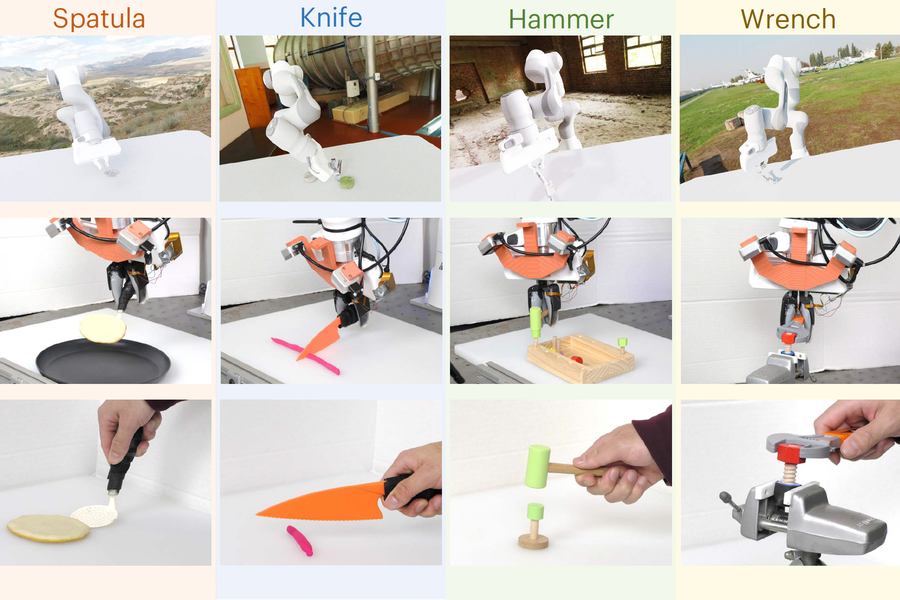
Previous image Next image
Let’s say you want to train a robot so it understands how to use tools and can then quickly learn to make repairs around your house with a hammer, wrench, and screwdriver. To do that, you would need an enormous amount of data demonstrating tool use.
Existing robotic datasets vary widely in modality — some include color images while others are composed of tactile imprints, for instance. Data could also be collected in different domains, like simulation or human demos. And each dataset may capture a unique task and environment.
It is difficult to efficiently incorporate data from so many sources in one machine-learning model, so many methods use just one type of data to train a robot. But robots trained this way, with a relatively small amount of task-specific data, are often unable to perform new tasks in unfamiliar environments.
In an effort to train better multipurpose robots, MIT researchers developed a technique to combine multiple sources of data across domains, modalities, and tasks using a type of generative AI known as diffusion models.
They train a separate diffusion model to learn a strategy, or policy, for completing one task using one specific dataset. Then they combine the policies learned by the diffusion models into a general policy that enables a robot to perform multiple tasks in various settings.
In simulations and real-world experiments, this training approach enabled a robot to perform multiple tool-use tasks and adapt to new tasks it did not see during training. The method, known as Policy Composition (PoCo), led to a 20 percent improvement in task performance when compared to baseline techniques.
“Addressing heterogeneity in robotic datasets is like a chicken-egg problem. If we want to use a lot of data to train general robot policies, then we first need deployable robots to get all this data. I think that leveraging all the heterogeneous data available, similar to what researchers have done with ChatGPT, is an important step for the robotics field,” says Lirui Wang, an electrical engineering and computer science (EECS) graduate student and lead author of a paper on PoCo .
Wang’s coauthors include Jialiang Zhao, a mechanical engineering graduate student; Yilun Du, an EECS graduate student; Edward Adelson, the John and Dorothy Wilson Professor of Vision Science in the Department of Brain and Cognitive Sciences and a member of the Computer Science and Artificial Intelligence Laboratory (CSAIL); and senior author Russ Tedrake, the Toyota Professor of EECS, Aeronautics and Astronautics, and Mechanical Engineering, and a member of CSAIL. The research will be presented at the Robotics: Science and Systems Conference.
Combining disparate datasets
A robotic policy is a machine-learning model that takes inputs and uses them to perform an action. One way to think about a policy is as a strategy. In the case of a robotic arm, that strategy might be a trajectory, or a series of poses that move the arm so it picks up a hammer and uses it to pound a nail.
Datasets used to learn robotic policies are typically small and focused on one particular task and environment, like packing items into boxes in a warehouse.
“Every single robotic warehouse is generating terabytes of data, but it only belongs to that specific robot installation working on those packages. It is not ideal if you want to use all of these data to train a general machine,” Wang says.
The MIT researchers developed a technique that can take a series of smaller datasets, like those gathered from many robotic warehouses, learn separate policies from each one, and combine the policies in a way that enables a robot to generalize to many tasks.
They represent each policy using a type of generative AI model known as a diffusion model. Diffusion models, often used for image generation, learn to create new data samples that resemble samples in a training dataset by iteratively refining their output.
But rather than teaching a diffusion model to generate images, the researchers teach it to generate a trajectory for a robot. They do this by adding noise to the trajectories in a training dataset. The diffusion model gradually removes the noise and refines its output into a trajectory.
This technique, known as Diffusion Policy , was previously introduced by researchers at MIT, Columbia University, and the Toyota Research Institute. PoCo builds off this Diffusion Policy work.
The team trains each diffusion model with a different type of dataset, such as one with human video demonstrations and another gleaned from teleoperation of a robotic arm.
Then the researchers perform a weighted combination of the individual policies learned by all the diffusion models, iteratively refining the output so the combined policy satisfies the objectives of each individual policy.
Greater than the sum of its parts
“One of the benefits of this approach is that we can combine policies to get the best of both worlds. For instance, a policy trained on real-world data might be able to achieve more dexterity, while a policy trained on simulation might be able to achieve more generalization,” Wang says.
Because the policies are trained separately, one could mix and match diffusion policies to achieve better results for a certain task. A user could also add data in a new modality or domain by training an additional Diffusion Policy with that dataset, rather than starting the entire process from scratch.
The researchers tested PoCo in simulation and on real robotic arms that performed a variety of tools tasks, such as using a hammer to pound a nail and flipping an object with a spatula. PoCo led to a 20 percent improvement in task performance compared to baseline methods.
“The striking thing was that when we finished tuning and visualized it, we can clearly see that the composed trajectory looks much better than either one of them individually,” Wang says.
In the future, the researchers want to apply this technique to long-horizon tasks where a robot would pick up one tool, use it, then switch to another tool. They also want to incorporate larger robotics datasets to improve performance.
“We will need all three kinds of data to succeed for robotics: internet data, simulation data, and real robot data. How to combine them effectively will be the million-dollar question. PoCo is a solid step on the right track,” says Jim Fan, senior research scientist at NVIDIA and leader of the AI Agents Initiative, who was not involved with this work.
This research is funded, in part, by Amazon, the Singapore Defense Science and Technology Agency, the U.S. National Science Foundation, and the Toyota Research Institute.
Share this news article on:
Related links.
- Project website
- Edward Adelson
- Russ Tedrake
- Computer Science and Artificial Intelligence Laboratory
- Department of Electrical Engineering and Computer Science
- Department of Mechanical Engineering
- Department of Aeronautics and Astronautics
- Department of Brain and Cognitive Sciences
Related Topics
- Artificial intelligence
- Computer science and technology
- Mechanical engineering
- Computer Science and Artificial Intelligence Laboratory (CSAIL)
- Electrical Engineering & Computer Science (eecs)
- Aeronautical and astronautical engineering
- Brain and cognitive sciences
- National Science Foundation (NSF)
Related Articles

Method rapidly verifies that a robot will avoid collisions

A new optimization framework for robot motion planning

AI helps robots manipulate objects with their whole bodies
Soft robots that grip with the right amount of force
Previous item Next item
More MIT News
Study: Titan’s lakes may be shaped by waves
Read full story →
3 Questions: Catherine D’Ignazio on data science and a quest for justice
Microscope system sharpens scientists’ view of neural circuit connections

Arvind, longtime MIT professor and prolific computer scientist, dies at 77

MIT-Takeda Program wraps up with 16 publications, a patent, and nearly two dozen projects completed

David Autor named the inaugural Daniel (1972) and Gail Rubinfeld Professor in Economics
- More news on MIT News homepage →
Massachusetts Institute of Technology 77 Massachusetts Avenue, Cambridge, MA, USA
- Map (opens in new window)
- Events (opens in new window)
- People (opens in new window)
- Careers (opens in new window)
- Accessibility
- Social Media Hub
- MIT on Facebook
- MIT on YouTube
- MIT on Instagram
- Communication Systems
- Mobile Communications
- Engineering
- Communication Engineering
- Optical Engineering
4G, 5G, 6G, 7G and Future Mobile Technologies
- February 2021
- American Journal of Computer Science and Technology 9(2):75

- Griffith University
Abstract and Figures

Discover the world's research
- 25+ million members
- 160+ million publication pages
- 2.3+ billion citations
- Sandeep Bhatia

- Devraj Gautam
- Soniya Verma

- Norbert Ludant

- Jatinder Kaur
- Vishal Kumar
- Kunwar Singh Vaisla

- Fanuel Melak Asmare

- K. Annapoorneshwari Shetty
- Subrahmanya Bhat
- V. I. Blanutsa
- Selo Sulistiyo
- Sigit B. Wibowo
- Hary Nur Hodayat
- Kaan CÖMERT
- Mustafa AKKAŞ
- Yashuang Yi
- Jiangyuan Gu

- L. Leema Priyadharshini
- P. S. M. Tripathi
- Ramjee Prasad
- S R Tripathi
- K P Sucheta P Yadav
- Ajay Kachhavay
- Recruit researchers
- Join for free
- Login Email Tip: Most researchers use their institutional email address as their ResearchGate login Password Forgot password? Keep me logged in Log in or Continue with Google Welcome back! Please log in. Email · Hint Tip: Most researchers use their institutional email address as their ResearchGate login Password Forgot password? Keep me logged in Log in or Continue with Google No account? Sign up

IMAGES
VIDEO
COMMENTS
Abstract: Third generation (3G) mobile networks faces a ne w rival; so called 4G. An. astonishingly new network may be even more profitable. The goal of 4G is to replace the. current proliferation ...
the first commercia l 3G network in Japa n in Oct. 2001. 4G: 4G, the fourth-generation of wireless service, is an. enhancement from 3G a nd is presently the most extensive, widespread, expedit ...
Driven by the growing demand for quality assured mobility; new promising technologies have emerged, such as 4G and 5G networks, in order to meet users' needs. Indeed, 4G networks unceasingly seek to improve the offered services and to guarantee a certain level of quality of service (QoS) for users while moving with high speeds. On his side, 5G standard is on its way. Promising superfast speeds ...
This research paper presents an overview of 4G technology trends in the wireless technology market, a comparative overview of 4G v/s previous generation technologies it's architecture and its ...
This paper explores the network architecture of 4G (4th Generation) and LTE (Long Term Evolution) wireless technologies, the mobile standards used by these technologies and key features, and the future of mobile communications in the longer term. — he earlier evolution of broadband wireless technologies is the consequence of growing demand in the world for best ever mobile Internet access ...
The purpose of the research is a detailed study on 3G, 4G, and 5G network technologies. Published in: 2017 Second International Conference on Recent Trends and Challenges in Computational Models (ICRTCCM) Article #: Date of Conference: 03-04 February 2017. Date Added to IEEE Xplore: 05 October 2017. ISBN Information:
Abstract. Based on the analysis of 4G communication network structure and key technologies, this paper expounds the 4 (6) communication structure, and studies the basic characteristics of 4G communication network, including: high speed, large capacity, the coexistence of different types of users, strong compatibility and flexibility, and the ...
Challenges. Hassan Gobjuka. Verizon. 919 hidden Ridge. Irving, TX 75038. Abstract. With the major wireless service providers planning to start deployment of 4G wireless networks by mid 2010, research and industry communities are racing against time to find solutions for some of the prominent still open. issues in 4G networks.
In the previous several years, wireless telecommunications technology has seen a significant change. The term "generation" in the context of wireless communication typically describes to a shift in the essential characteristics of the assistance being offered, such as transmission technologies, bit rates, frequency bands, channel frequency bandwidth, and data transfer capacity. One of the ...
In addition, the paper highlights the review of the technologies implemented for 4G and 5G mobile networks. Cellular networks have grown and improved immensely in recent years, in terms of customers, data speeds, outreached and other aspects. In both 4G and 5G technology, the mobile consumer has taken precedence above all others.
The 4G wireless system, its architecture, security services, benefits and challenges of 4G wireless technology, assures the high mobility with high level speed of data rates and high capacity IP based services and application. . ABSTRACT Mobile Communication has been developed rapidly since last few decades. The growth of the wireless broadband technologies in the modern years was the answer ...
This paper discusses the different communication technologies present in the current communication system and coming in future 2020. The next evolution in the communication industry is coming 5G communication system that will start in approx. 2020. ... 4G, 5G, and 6G technology. The highest data rate of 6G is 70 Gbps, whereas the lowest data ...
The existence of 4G technologies is the indicator or valid proof of the rapid and massive growth of wireless communication technologies, which is propagated through 1G, 2G and 3G technology and 5G as an upcoming technology.4G networks are introduced with the main intention of customization of a flexible and ubiquitous service provision in the middle of 2012 based on digital broadband packet ...
Through a journey which started. about 40 years ago, cellular commu-. nications have experienced dramatic. changes and upgrades from 1G to 4G. Those transitions include the system. change from ...
This paper is focused on the specification of future generations of wireless mobile communication networks. The paper throws light on the evolution and development of various generations of mobile wireless technology along with their significance and advantages of one over the other. 5G technologies will change the way most high-bandwidth users access their phones.
This paper gives an overview of the Long Term Evolution (LTE) of the Universal Mobile Telecommunication System (UMTS), which is being developed by the 3rd Generation Partnership Project (3GPP). LTE constitutes the latest step towards the 4th generation (4G) of radio technologies designed to increase the capacity and speed of mobile communications. Particular attention is given to the ...
market. Under these circumstances, this paper will present about the current trends and its underlying technologies to implement the 4G mobile technology. This paper also shows some of the possible scenarios that will benefit the 4th generation technology. Keywords 4G Mobile Technologies, 3GPP Long Term Evolution, WiMAX,
Feature papers represent the most advanced research with significant potential for high impact in the field. A Feature Paper should be a substantial original Article that involves several techniques or approaches, provides an outlook for future research directions and describes possible research applications. ... "Impact of 3G and 4G Technology ...
1. Introduction. Most recently, in three decades, rapid growth was marked in the field of wireless communication concerning the transition of 1G to 4G [1,2].The main motto behind this research was the requirements of high bandwidth and very low latency. 5G provides a high data rate, improved quality of service (QoS), low-latency, high coverage, high reliability, and economically affordable ...
4G and 5G technologies: A Comparative Study. September 2020. DOI: 10.1109/ATSIP49331.2020.9231605. Conference: 2020 5th International Conference on Advanced Technologies for Signal and Image ...
Abstract: The purpose of this study is to identify the latest trends in Mobile communication, which is continuously one of the hottest areas that are developing at a booming speed, with advanced techniques emerging in all the fields of mobile and wireless communications. Current times are just the beginning for deploying 4G mobile communication ...
The European Defence Agency (EDA) is delighted to announce the three winners of its Research, Technology, and Innovation Papers Award 2024. This year, the competition focused on innovative technologies, processes, and applications for enhanced future defence capabilities. The three winners were presented with their awards at Eurosatory in Paris ...
Purvansh Bhatia, a recent graduate of BASIS Scottsdale, has already accomplished an impressive feat by having a research paper published. ... SDG 04 Quality Education Tempe campus School of Earth and Space Exploration Science and technology Undergraduate research Science Space exploration Research The College of Liberal Arts and Sciences.
standard. 5G will provide better speeds and coverage than the current 4 G. 5G operates with a 5 GHz signal and. is set to offer speeds of up to 1 Gb/s for tens of connections or tens of Mb/s for ...
PoCo is a solid step on the right track," says Jim Fan, senior research scientist at NVIDIA and leader of the AI Agents Initiative, who was not involved with this work. This research is funded, in part, by Amazon, the Singapore Defense Science and Technology Agency, the U.S. National Science Foundation, and the Toyota Research Institute.
In this paper an attempt has been made to provide a study of different cellular technologies namely 4G, 5G, 6G, 7G, and FG respectively and detail comparison among them. Basic LTE interfaces. E ...